30 Common Types of Cyber Attacks and How to Prevent Them



Join thousands of professionals and get the latest insight on Compliance & Cybersecurity.


In today's digital age, cybersecurity threats are a constant and evolving concern for individuals, businesses, and organizations alike. Cybercriminals employ a wide range of tactics and techniques to gain unauthorized access, steal data, disrupt operations, or demand ransom payments. Understanding these threats is crucial for implementing effective defense strategies.
This comprehensive guide provides an overview of 30 common cyberattacks, their characteristics, and potential consequences.
What is a cyberattack?
Cyberattack refers to an intentional or malicious attempt taken to gain unauthorized access to an organization network or systems, to steal, destroy or misuse data. Some examples of cyber attacks include ransomware, malware injection, phishing attacks, social engineering scams, password theft, denial of service attacks (DoS) etc.
Why do people launch cyber attacks?
People launch cyber attacks for various reasons. The motive might be personal, such as disgruntled employees seeking retribution by stealing money, data or disrupting the systems. Or, for financial gain, stealing sensitive credit card information, for monetary extortion or identity theft. The motive can also be political or corporate espionage, engaging in cyber warfares where intellectual property or government secrets are exploited. Or performing hacktivism for simply showing off skills.
Who do cyberattackers target?
Cyber attacks target a wide range of entities from individual users, businesses of all sizes, government organizations, healthcare providers, NGOs, celebrities and educational institutions. Cyber threat actors often choose targets based on the motive, perceived vulnerabilities, existing security measures and the extent of access to sensitive information.
How often do cyber attacks occur?
According to a report by University of Maryland, a cyber attack occurs every 39 seconds amounting to approximately 2200 a day. The frequency highlights the relentless nature of cyber threats and emphasizes the requirement for organizations to implement robust cybersecurity measures.
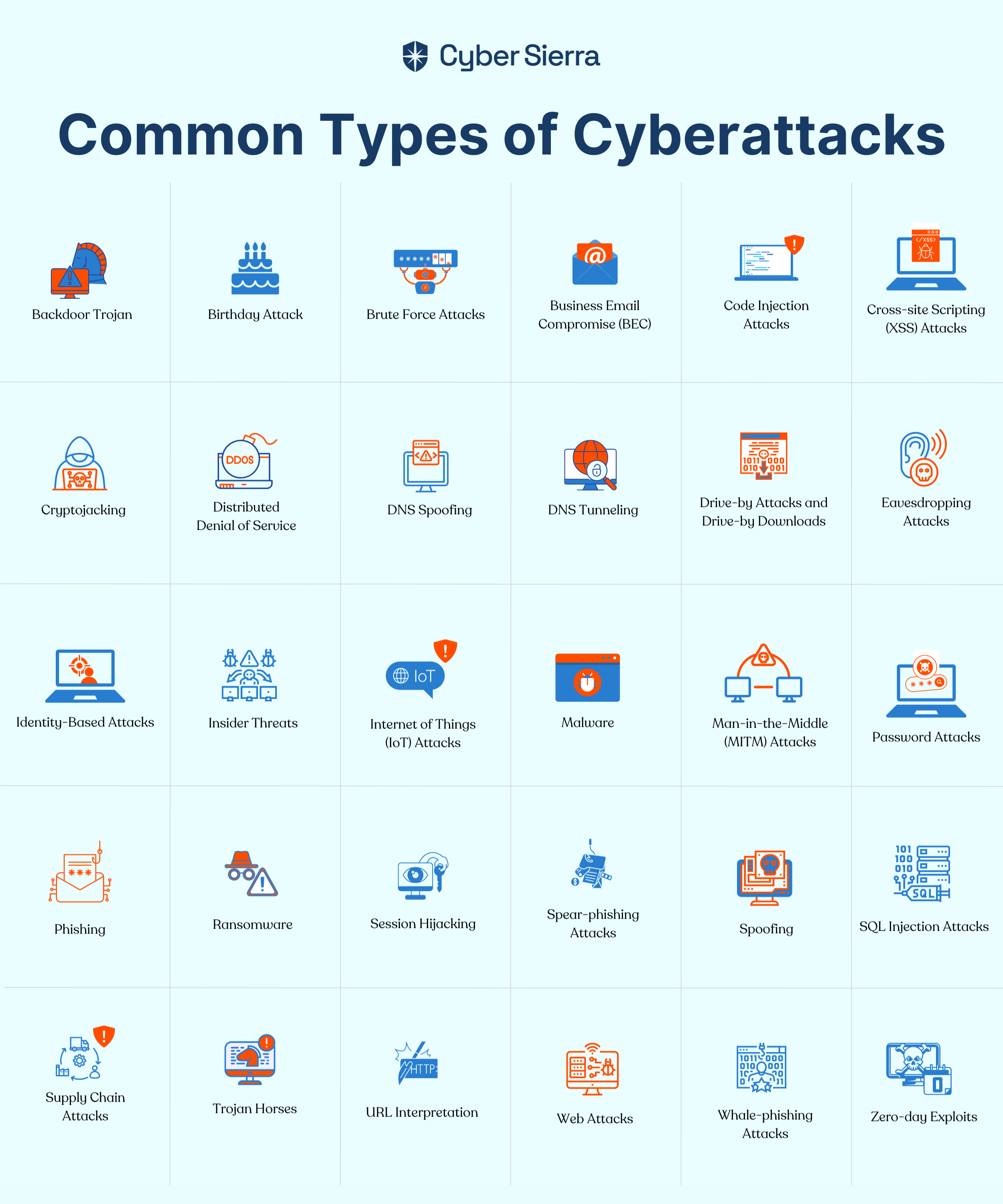
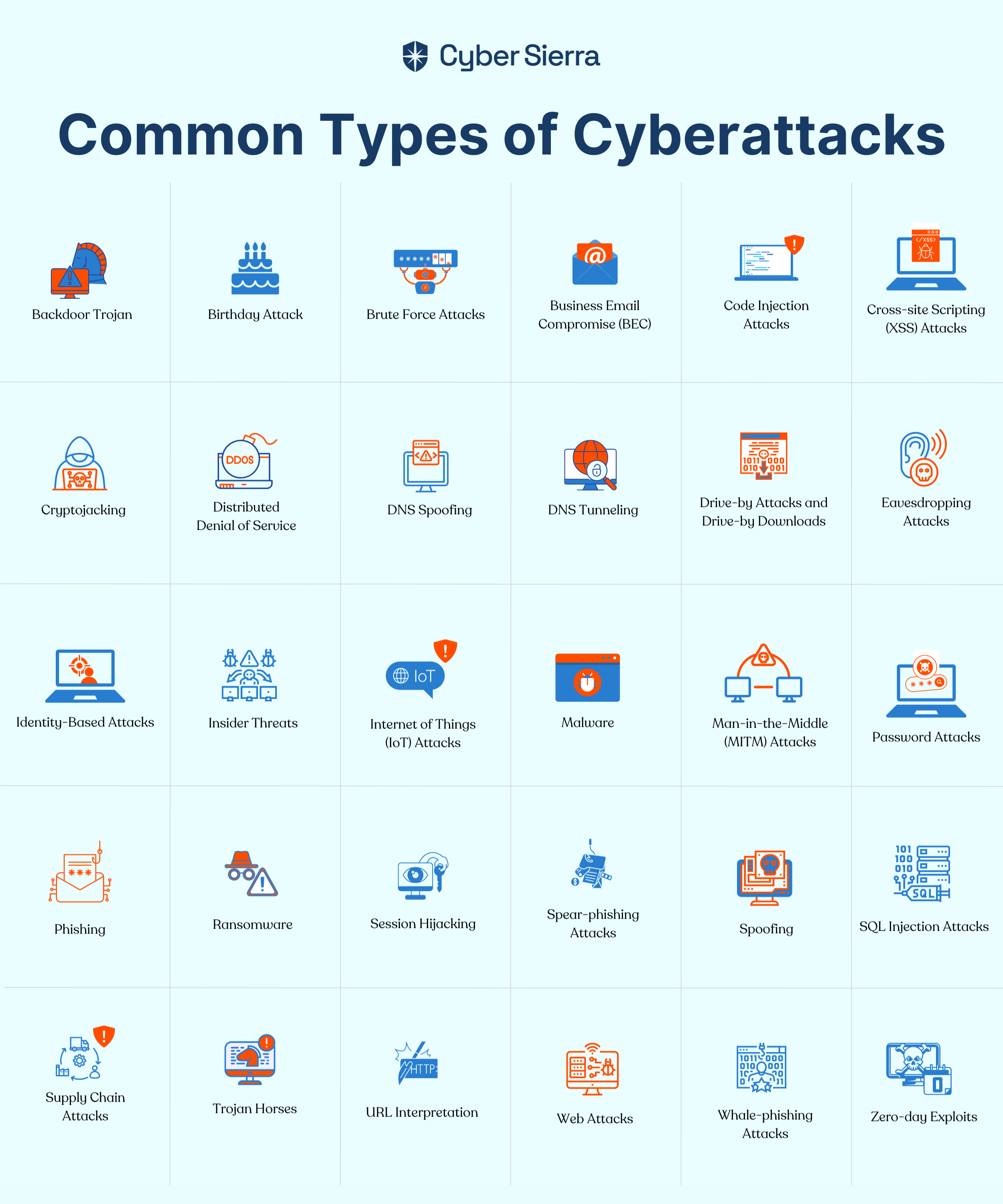
Common Types of Cyber Attacks
Some of the common types of cyber attacks are malware attacks, phishing, SQL injection attacks, ransomware, man-in-the-middle attacks and distributed denial of service (DDoS).
These cybersecurity attacks, however, are not limited to large enterprises alone. Malicious actors often exploit any internet-connected device, making it a potential weapon or target. This makes small and medium-sized businesses (SMBs), which often have less robust cybersecurity measures in place, also vulnerable to various security incidents.
Security professionals and their teams, therefore, must be prepared to counter a wide range of cyber attacks. To aid in this effort, we will discuss 30 of the most common yet damaging types of cyber attacks and how they work.
Backdoor Trojan
Backdoor trojans are malicious software that creates a hidden entry point for authorized access to launch a remote attack into a system or network. Once installed, cybercriminals can control the compromised system, steal data, monitor user activities, or launch further attacks. Backdoor trojans can be distributed through phishing mails, malicious websites, or through software vulnerabilities.
These attacks remain undetected to traditional antivirus softwares making them a significant threat. Implementing robust cyber security practices and keeping systems patched and exercising caution against unsolicited programs is crucial to prevent such attacks.
Birthday Attack
A birthday attack is a type of cryptographic attack or a collision attack that exploits the mathematics behind the birthday probability theory of finding collisions in the output of cryptographic hash functions.
In this context the attack aims to find the hash function by generating a large number of inputs, and find two inputs that produce the same hash value. This compromises the security of systems relying on hash uniqueness such as digital signatures or data encryption.To stay safe use hash functions with large output spaces and consider techniques like salting to enhance security.
Brute Force Attacks
A brute force attack is a hacking technique where attackers systematically guess every possible combination of characters to passwords, encryption keys, or other authentication mechanisms through trial and error method until they hit upon unauthorized access into systems.
It is considered as a favored strategy among hackers due to its reliability and effectiveness of cracking weak and poorly implemented security systems. To mitigate brute force attacks enabling strong lengthy passwords, secure encryption with key stretching algorithms, rate limiting failed attempts and account lockouts for incorrect guesses are suggested.
Business Email Compromise (BEC)
BEC attacks refers to a type of phishing attack where cybercriminals utilize email accounts and impersonate as executive-level employees or trusted business partners to trick victims into transferring funds or disclosing sensitive information via email. BEC accounts often target employees responsible for financial transactions or sensitive data.
To mitigate the risk of BEC attacks, organizations should implement stringent security measures such as 2FA and email authentication protocols, conducting employee training and awareness programs, and verification procedures for financial transactions.
Code Injection Attacks
As the name indicates, Code injection refers to an attack where malicious code is inserted into a web application or software allowing attackers to gain control of the system or access sensitive data.Code injection poses serious threats potentially leading to catastrophe outcomes such as spread of computer virus or worms. It can be in the form of SQL injection, or command injection depending on the vulnerability. These vulnerabilities arise when an application passess untrusted data to the interpreter.
To defend against code injection attacks implement secure coding practices, web application firewalls, intrusion detection systems, and regularly update and patch software to identify gaps and vulnerabilities.
Cross-site Scripting (XSS) Attacks
Cross-site Scripting (XSS) is a type of attack that allows attackers to inject malicious side scripts into trusted web based applications. These scripts are executed by the victim's web browser to hijack user sessions, steal cookies, or redirect users to malicious sites. There are different types of XSS such as reflected XSS, stored XSS, AND DOM based XSS each targeting different parts of the web application.
To mitigate XSS attacks web developers should implement proper input validation, output coding, and content security policies (CPSs). Also, web security firewalls and regular security audits can help detect and prevent XSS vulnerabilities.
Cryptojacking
Cryptojacking is a cyber attack where hackers hijack a victim's computing resources to secretly mine cryptocurrency without their knowledge or consent, resulting in compromised performance and increased energy costs. The profits generated from this mining are directly to the hacker cryptocurrency wallet. Before its shutdown in March 2019, Coinhive emerged as a prominent tool for cryptojacking, being utilized in such incidents.
To mitigate this users should regularly update software, use ad blockers and antivirus programs, and employ intrusion detection systems.
Distributed Denial of Service
A distributed denial-of-service (DDoS) is a type of attack where an attacker floods the targeted server, service, or network by overwhelming it or its surrounding infrastructure with a flood of internet traffic from multiple users making it unavailable to other users or disrupting normal operations.
In Oct 2016, Dyn, a major DNS provider faced a record DDoS attack reaching 1.5 terabits per second. This assault disrupted services for websites like Twitter, Netflix, Paypal highlighting severity of the DDoS attacks and the importance of implementing robust strategies. Utilizing traffic filtering and cloud-based real-time monitoring tools can block suspicious traffic patterns and help minimize DDosS and ensure protection for your network.
DNS Spoofing
Domain Name System (DNS) spoofing is also called DNS cache poisoning where the attacker targets the DNS servers and redirects legitimate web traffic to malicious websites.
This is done by exploiting vulnerabilities in the DNS protocol or by corrupting the DNS cache leading to phishing scams and malware attacks. Implementing (Domain System Security Extensions) DNSSEC and DNS resolvers can minimize the risk of DNS spoofing and ensure authenticity of DNS responses.
DNS Tunneling
DNS tunneling is a technique used by attackers to bypass firewalls and security controls by encoding unauthorized data or commands within DNS queries and responses making them look like legitimate DNS traffic.
Utilizing DNS sinkholing techniques and deep packet infections help analyze anomalies in DNS traffic and redirect to a controlled servier and helps prevent unauthorized access.
Drive-by Attacks and Drive-by Downloads
Drive-by attacks refers to an automatic malware download in web browsers or browser plugins that is unaware to the users, compromising the systems and leaving the victim vulnerable for cyber attacks. In 2016, the Angler Exploit Kit, a type of drive-by attack toolkit, was used to target Adobe Flash and Microsoft Silverlight, and Java leading to the widespread distribution of ransomware and other malware.
Ensuring that web browsers, installed plugins and applications are regularly updated. Employ ad blocking and anti malware tools to prevent these types of download.
Eavesdropping Attacks
Eavesdropping, also called as sniffing, is a type of attack where the attackers intercept, monitor, modify or delete data. This is done by compromising unsecured network traffic or communications without authorization, potentially exposing sensitive data.
To mitigate these types of attacks it is suggested to utilize strong encryption methods, implementing network segmentation, and educating users on secure communication practices.
Identity-Based Attacks
Identity-based attacks are a form of social engineering where cybercriminals target user identities and credentials to gain unauthorized access to systems or data. These attacks can take various forms, such as phishing, credential stuffing, password spraying, or account takeover attempts.
Establishing comprehensive, Identity and Access Management (IAM) solutions to control user identities, access privileges, and authentication processes, reducing the risk of unauthorized access.
Insider Threats
Insider threats are cyber security risks that involve malicious activities by authorized users or individuals within an organization, such as disgruntled employees or contractors, who abuse their access privileges to steal data, sabotage systems, or conduct other harmful activities.
In 2013, Edward Snowden, a former NSA contractor, leaked classified information, revealing government surveillance programs. This breach of national security sparked global debates on privacy and surveillance, highlighting the risks of insider threats. Implementing role-based access control (RBAC) to restrict access to sensitive data, conducting regular employee monitoring can reduce the risk of insider threats.
Internet of Things (IoT) Attacks
IoT attacks target smart devices and applications exploiting vulnerabilities in their design or implementation to gain unauthorized access or control.
In 2016, the Mirai botnet attack targeted vulnerable IoT devices, such as routers, IP cameras, and DVRs, by exploiting default passwords and insecure configurations. Regularly updating device firmware and applying security patches to address known vulnerabilities can enhance the security posture of IoT devices.
Malware
Malware attack, short for malicious software, is a common cyber attack designed to disrupt systems, steal data, or gain unauthorized access. Examples of malware include harmful code, viruses, worms, Trojans, ransomware, and spyware.
Enabling a multi-layered approach, implementing antivirus protection, regular software updates, and user awareness training, can reduce the risk of malware attacks.
Man-in-the-Middle (MITM) Attacks
MITM attacks also known as an on-path attack involves intercepting and potentially modifying communications between two parties, allowing attackers to eavesdrop on or manipulate the exchanged data.
In 2018, researchers discovered a vulnerability in the Starbucks mobile app that allowed attackers to conduct MITM attacks on customers using the company's public Wi-Fi networks. The vulnerability enabled the attackers to intercept and potentially modify the communication between the app and Starbucks' servers, potentially exposing sensitive user information. By adopting security measures, like encryption, network segmentation, and continuous monitoring, organizations and individuals can significantly reduce the risk of falling victim to MITM attacks.
Password Attacks
Password attacks is a type of attack aimed to exploit password protected accounts by cracking or guessing user passwords through techniques like brute force, dictionary attacks, or exploiting password reuse or weak password policies.
In 2012, LinkedIn experienced a significant data breach where hackers exploited weak password encryption practices, resulting in the exposure of over 100 million user passwords. Enforce strong password requirements, regular password changes, implement MFA like SMS codes or biometric data to access their accounts can help mitigate these attacks.
Phishing
Phishing is a form of social engineering attack that involves tricking victims into revealing sensitive information, such as login credentials or financial data, through fraudulent emails, websites, or messages that appear legitimate.
In 2017, a phishing scam aimed at Google users sent fake Google Docs collaboration invites. Many fell for it, granting access to their google account and risking sensitive data exposure. Educating users about the common signs of phishing emails and implementing email filtering solutions and anti-phishing tools that can detect and block phishing emails reducing the likelihood of successful phishing attacks.
Ransomware
Ransomware is a type of cyber extortion technique attack that encrypts a victim's files or systems making them accessible, demanding a ransom payment in exchange for the decryption key.
One notable ransomware attack is the WannaCry ransomware attack that occurred in May 2017, affecting 250,000 users of Microsoft Windows across 150 countries. Maintain regular backups of critical data on separate, secure storage devices or cloud services to ensure that data can be restored without paying the ransom. Educate users about the risks of clicking on suspicious links, downloading attachments from unknown sources, and practicing safe browsing habits to prevent ransomware infections.
Session Hijacking
Session hijacking also known as cookie hijacking is a malicious attack that involves intercepting and taking control of an established user session, allowing attackers to impersonate the victim and gain unauthorized access to their accounts or data and is permitted to perform operations instead of the user whose session was hijacked.
Implementing secure communication protocols like HTTPS and utilize techniques such as session tokens, expiring sessions, and multi-factor authentication to enhance session security and reduce the risk of hijacking attempts.
Spear-phishing Attacks
Spear-phishing attacks are highly targeted phishing campaigns that target high profile individuals through malicious mails. The attacks use personalized information or social engineering tactics to increase the likelihood of a victim falling for the attack.
Conducting awareness training on phishing attempts, verifying sender authenticity and avoiding clicking on suspicious links or attachments. Also, implementing email filtering tools and email authentication protocols like SPF, DKIM, and DMARC can prevent such types of attacks.
Spoofing
Spoofing is a type of cyber attack where attackers impersonate a trusted source, such as a website, email address, or network entity, to deceive victims into revealing sensitive information or executing malicious actions.
These types of attacks can be mitigated by implementing robust authentication mechanisms, encryption, and educating users about the importance of verifying the legitimacy of sources before sharing sensitive information or taking action.
SQL Injection Attacks
SQL injection is a prevalent code injection tactic where attackers exploit vulnerabilities in web applications by inserting malicious SQL code into user input fields, allowing attackers to access or manipulate databases without proper authorization. Ensuring proper input validation and sanitation mechanism before using SQL queries can help prevent SQL injections.
Supply Chain Attacks
Supply chain is a type of attack where the attacker targets the elements in the software supply chain, introducing malicious code or vulnerabilities into legitimate software or hardware components, potentially compromising numerous systems and organizations downstream processes. One notable example is the 2020 SolarWinds attack where malicious code was injected into the software's build cycle, affecting about 18,000 downstream customers, including major firms and government agencies.
Implementing rigorous due diligence and vetting processes for third party suppliers and employing software integrity checks helps prevent these attacks.
Trojan Horses
Trojan horses is a type of malware that impersonates legitimate software or files, tricking users into installing it and granting unauthorized access or control to attackers.
This is done by inserting a malicious code in the software or the file attachment once downloaded the code executes to steal sensitive information. Utilizing antivirus software with real time monitoring capabilities exercising caution about downloading unknown files and phishing email can help mitigate these types of attacks.
URL Interpretation
URL interpretation also called as URL poisoning attacks are when an attacker exploits the way web browsers and servers interpret and handle URLs, allowing attackers to bypass security controls, conduct phishing attacks, or execute malicious code.
Implementing URL validation mechanisms, strong coding practices, input validation, and enforcing access controls help mitigate URL exploitation.
Web Attacks
Web attacks are a wide range of threats targeting web applications, such as cross-site scripting (XSS), SQL injection, and cross-site request forgery (CSRF). These attacks exploit vulnerabilities in the code or design of a web application allowing attackers to manipulate data and alter website content and steal sensitive information.
In 2017, Equifax, a major credit card company suffered a major data breach due to a web based vulnerability exposing personal information of 147 billion people. Implementing strict input validation mechanisms, conducting regular security audits, penetration testing helps prevent these types of attacks.
Whale-phishing Attacks
Whale-phishing attacks are targeted phishing attacks that focus on high-profile individuals or key executives within an organization, typically aiming to gain access to sensitive data or financial resources.
These attacks look more personalized and sophisticated since the attacks use social engineering tactics to make the profile look more credible for phishing which makes it difficult to bypass. Recommended mitigation strategies include employee infosec training, utilizing multi factor authentication, and using SIEM and end point detection tools.
Zero-day Exploits
Zero-day exploit is a cyber security vulnerability where the attackers take advantage of previously unknown vulnerabilities in a software application to compromise systems and steal sensitive information before a patch or solution is available. Since the vulnerability is not known to the vendor it is challenging to mitigate this. However performing regular software patches, implementing continuous monitoring, network segmentation and application whitelisting can help mitigate zero day attacks.
Next Steps - Adopt a Multi-layered Security Approach
(Design with the four pointers given below)
Defending against these diverse cybersecurity threats requires a multi-layered approach, including robust security measures, regular software updates, employee awareness training, and continuous monitoring and incident response capabilities to create a strong defense against cyber security threats.
Cultivating a Culture of Cyber Resilience
A multi-layered security approach ensures that each vulnerable area of the network is protected by multiple security controls that together bring a strong interconnected defined mechanism against potential attacks and enhances system, application , network, and infrastructure security.
By adopting this multi-layered security approach organization fosters a culture of cybersecurity awareness and resilience, to enhance their ability to defend against diverse threats. This holistic strategy empowers them to anticipate, withstand, and recover from cyber incidents, ensuring the continued protection of their critical assets and the trust of their customers and stakeholders.
Practicing Continuous Vigilance
Cybersecurity is an ongoing battle, requiring organizations to maintain a state of constant vigilance. Regular software updates and patches are essential to address known vulnerabilities and keep systems secure. Additionally, comprehensive employee security awareness training helps individuals recognize and respond to emerging threats, such as phishing and social engineering attacks.
Strengthening Incident Response Capabilities
Complementing these preventive measures, organizations should also invest in robust incident response capabilities. This includes implementing security monitoring tools, incident response plans, and dedicated security teams to quickly detect, investigate, and mitigate the impact of any successful cyber attacks.
Leverage automation for enhanced security
Understanding the nature and impact of cyber threats is crucial for organizations and individuals to prioritize cybersecurity efforts effectively. Implementing robust countermeasures to safeguard systems, data, and assets is paramount. However, considering the complexity of these systems, managing all these manually can be daunting. This is where the power of automation tools comes into play.
Utilizing automation tools protects your cyber assets, streamlines your operation, helps you track real-time monitoring of your cyber posture, automate proactive security measures and improves your indecent response capabilities thereby effectively mitigating cyber attacks.
Cybersecurity with Cyber Sierra
Cyber Sierra offers a comprehensive and integrated approach to cybersecurity, addressing security challenges both within the organization and across the extended ecosystem. Our platform streamlines governance, risk, and compliance for organizations, ensuring robust security practices and regulatory compliance.
The platform also features a robust Continuous Control Monitoring (CCM) functionality, which helps to continuously monitor security controls, rapidly detect and alert for deviations putting security controls on auto-pilot. The platform also offers threat intelligence by analyzing real-time data to help organizations stay ahead of emerging cyber threats.
Cyber Sierra's dedicated third-party risk management (TPRM) module assesses, monitors, and mitigates the vendor risk lifecycle. It also enables seamless risk transfer by integrating access to cyber insurance policies, allowing organizations to transfer unmitigated risks and ensure financial protection.
To see the platform live in action, schedule a demo today.



A weekly newsletter sharing actionable tips for CTOs & CISOs to secure their software.
Thank you for subscribing!
Please check your email to confirm your email address.
Find out how we can assist you in
completing your compliance journey.