The Proactive CISO’s Guide to MAS TRM Guidelines



Join thousands of professionals and get the latest insight on Compliance & Cybersecurity.
Where there’s sugar, expect unwanted ants.
That has proven true in Singapore. As the country grows into a world-renowned tech hub, it has become a sweet spot for innovative startups and enterprises. So has it for unwanted bad actors.
So much that, in 2022 alone, Singaporean financial institutions (FIs) spent a whopping US$5.7 billion fighting cybercrime and meeting regulations. In one massive phishing attack, for instance, Singapore’s OCBC Bank and its customers lost over US$10.8 million.
With no end to such cyberattacks in sight, more stringent cybersecurity compliance measures were needed. The Monetary Authority of Singapore (MAS) rightly stepped up to update its Technology Risk Management (TRM) Guidelines.
Updating the MAS TRM Guidelines was Necessary
The updated MAS TRM Guidelines adds another item to the already loaded to-dos of CISOs of banks and financial institutions (FIs). But given that cybercrime is getting worse, becoming (and staying) compliant is necessary to help your team achieve cyber resilience.
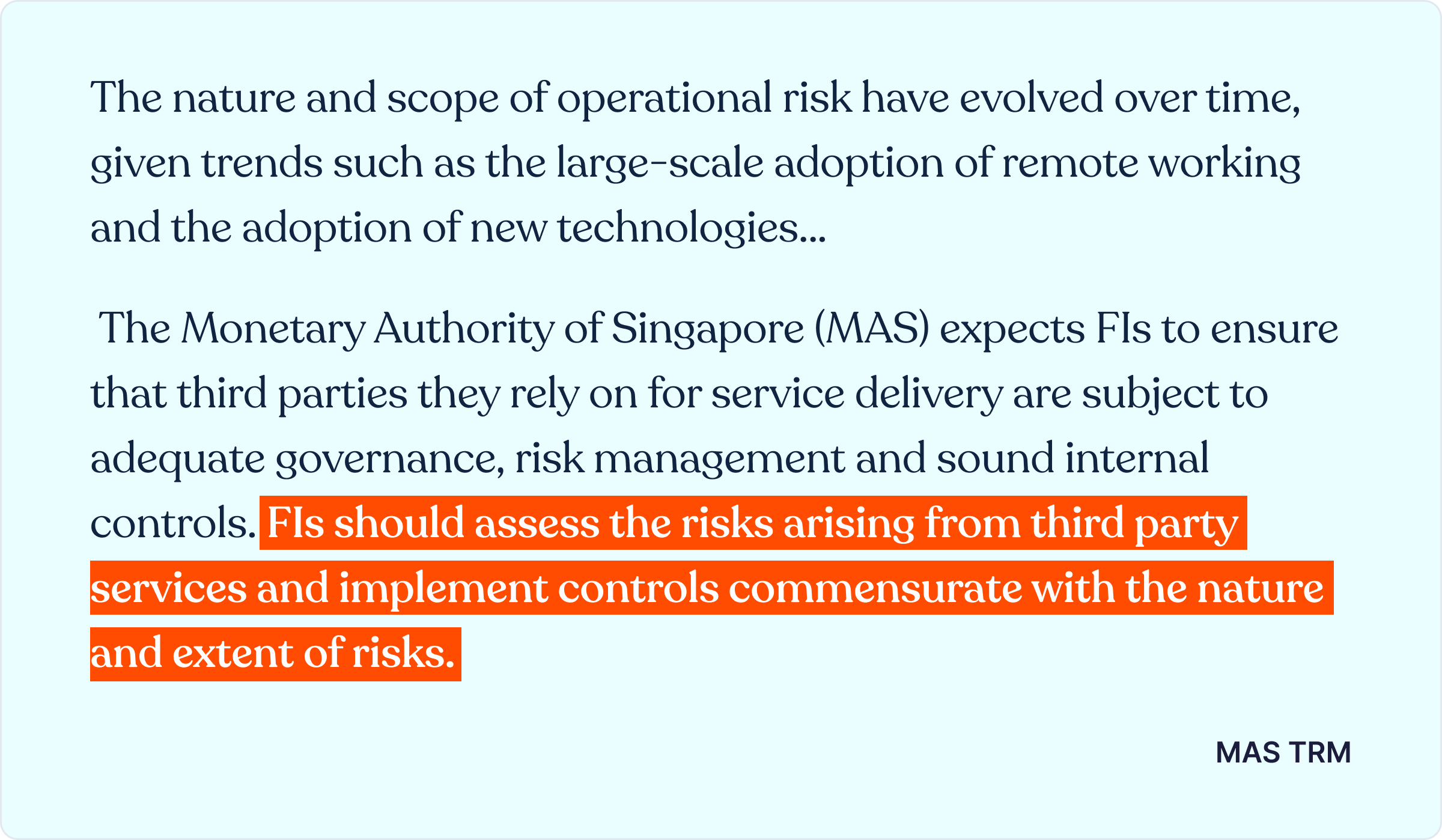
According to the regulatory body:
In other words, threat actors are now more sophisticated. The dire situation means MAS TRM Guidelines helps banks, FIs, and all enterprises working with them to:
- Understand their company’s exposure to technology risks.
- Ensure IT and cyber resilience by erecting robust risk management frameworks across their company’s operations.
But achieving both can be overwhelming.
What’s even more troubling is the fact that to remain compliant with Singapore’s MAS TRM Guidelines, companies are required to monitor cybersecurity controls continuously. For this, you need a smart enterprise compliance automation suite that automates mundane steps involved.
That’s where a platform like Cyber Sierra comes in.
And in this piece, you’ll see how it automates the process of becoming (and staying) compliant with MAS TRM Guidelines.
Before we dive in…
Becoming (and Staying) Compliant with MAS TRM Guidelines
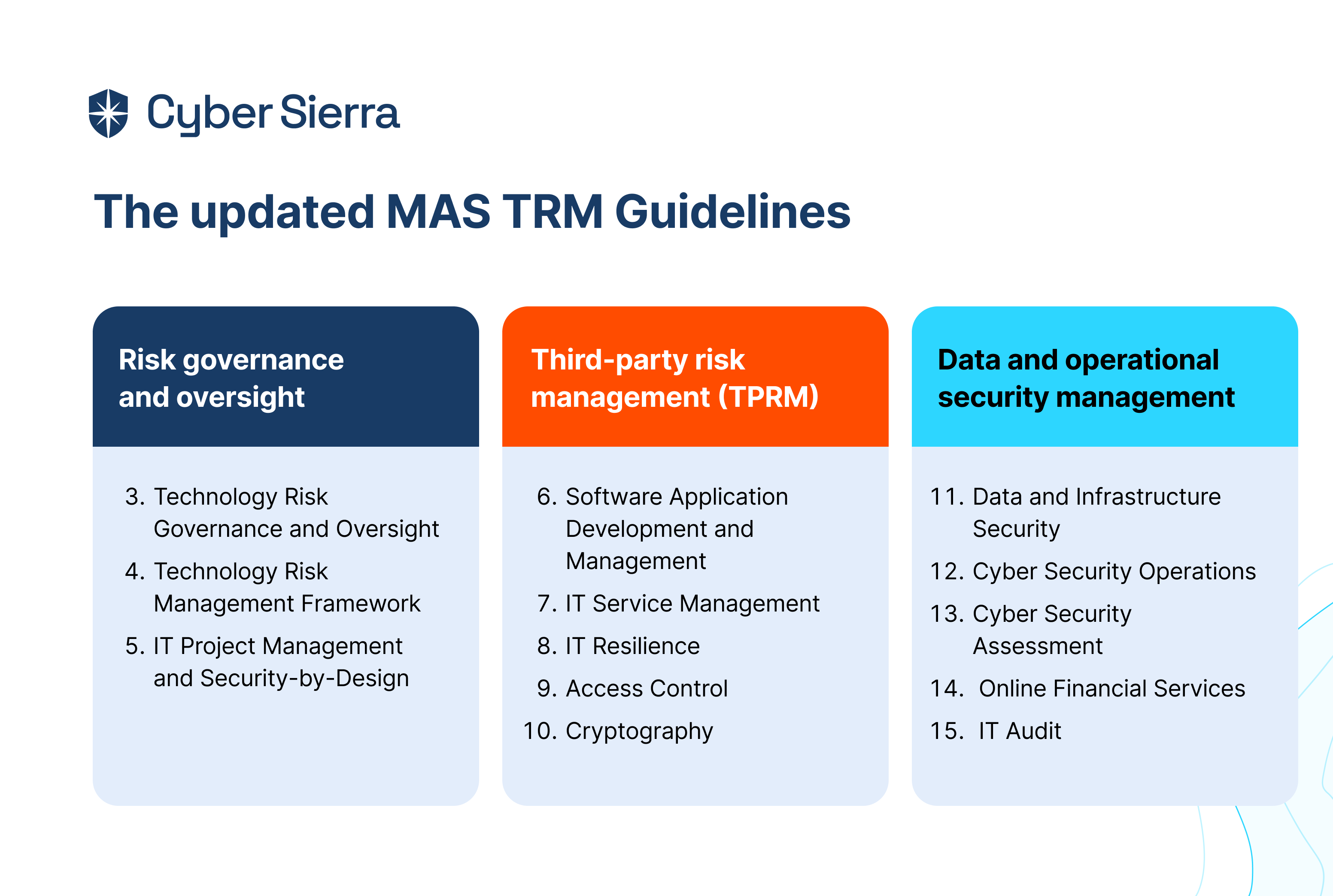
The updated MAS TRM Guidelines has fifteen sections:
- Preface
- Application of MAS TRM Guidelines
- Technology Risk Governance and Oversight
- Technology Risk Management Framework
- IT Project Management and Security-by-Design
- Software Application Development and Management
- IT Service Management
- IT Resilience
- Access Control
- Cryptography
- Data and Infrastructure Security
- Cyber Security Operations
- Cyber Security Assessment
- Online Financial Services
- IT Audit
The first and second sections provide an overview of the MAS TRM Guidelines. After that, each section from 3–15 has subsections outlining best practices organizations should follow to become and stay compliant. But as illustrated below, after reviewing all these sections and subsections, we grouped them into three critical areas:
- Risk governance and oversight
- Third-party risk management (TPRM)
- Data and operational security management.
Risk Governance and Oversight
Sections under this area of the MAS TRM Guidelines outline the personnel and frameworks needed to ensure that a technology risk management strategy is established and implemented. The emphasis is first on having a more extensive list of roles appointed into your organization’s board of directors and senior management.
The regulatory body notes:
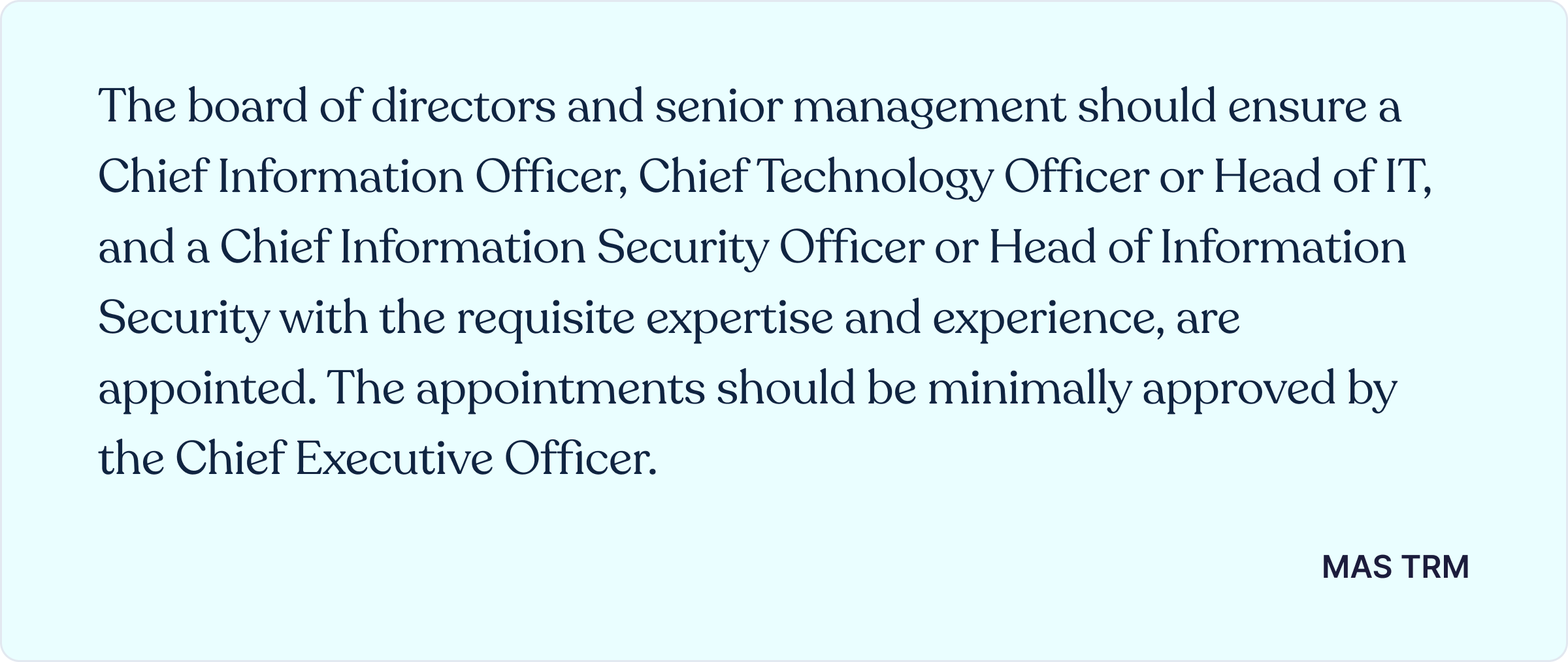
The importance of these roles can’t be overstretched.
Their combined expertise is needed to oversee the creation and implementation of technology risk management and IT project management frameworks, respectively. Once these personnels have been appointed, it’s best to have them working collaboratively.
That’s where an interoperable cybersecurity platform like Cyber Sierra comes in. Our platform gives you a central place to work collaboratively and implement the needed security frameworks:
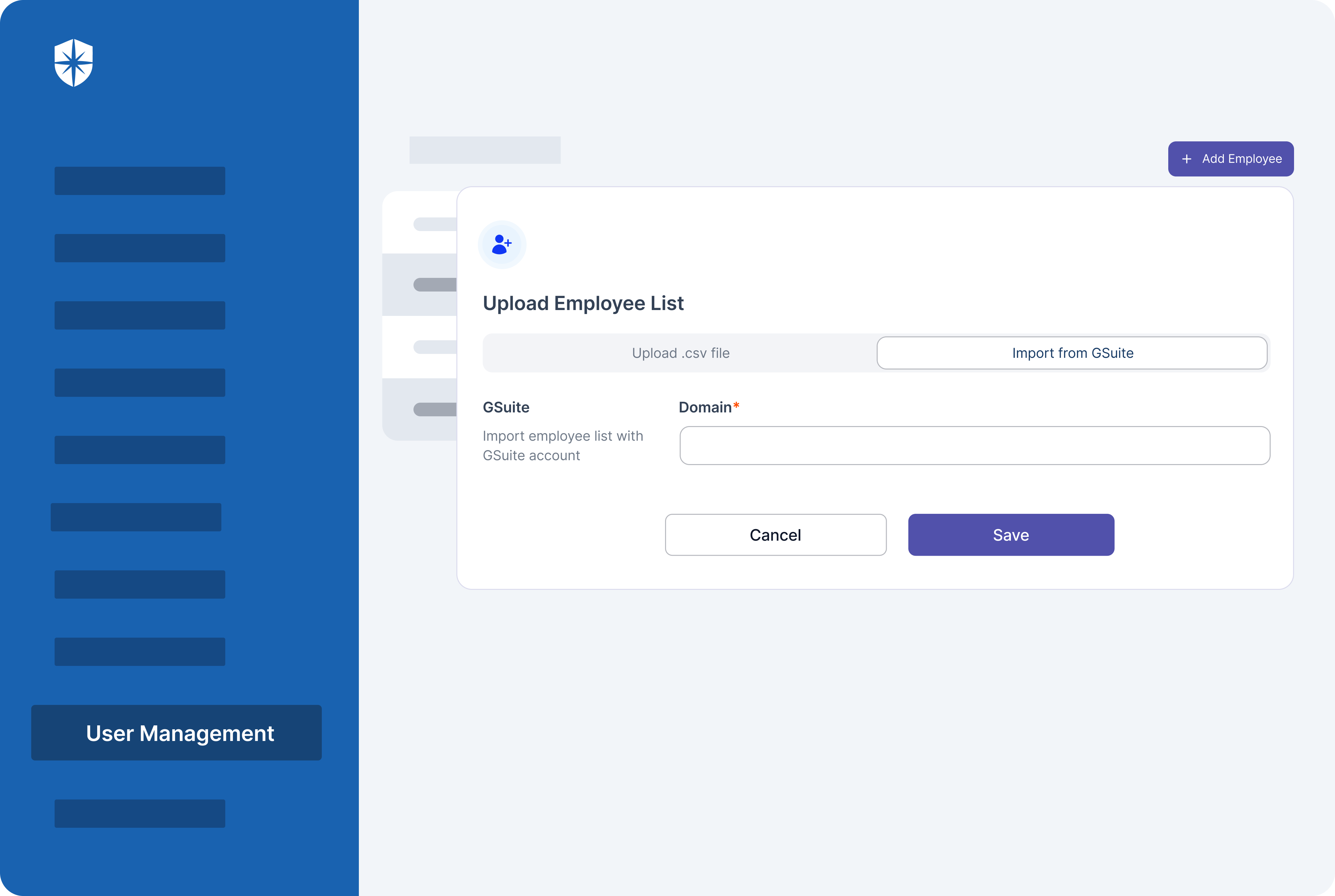
As shown, you can add appointed executives for more streamlined collaboration based on their roles. This automatically gives them role-based access controls for overseeing:
- The implementation of technology risk management strategy
- The erection of a third-party risk management framework
- The continuous assessment, management, and remediation of threats and risk necessary to remain compliant.
One benefit of having them collaborate from a streamlined platform like Cyber Sierra is that besides the ease of assigning policies and security controls to them, they’ll work together from a single pane.
More on that as we proceed.
Third-Party Risk Management (TPRM)
Sections 6–10 of the MAS TRM Guidelines, if you look closely, have a lot to do with 3rd party vendor risks. This is probably why the most recent update focuses mainly on third-party risk management. According to the regulatory body, this renewed focus is because:
By this recommendation, assessing risks from 3rd-parties should be prioritized. To do this effectively, it’s best to start by categorizing vendors based on their access to your organization’s sensitive data.
As illustrated below:
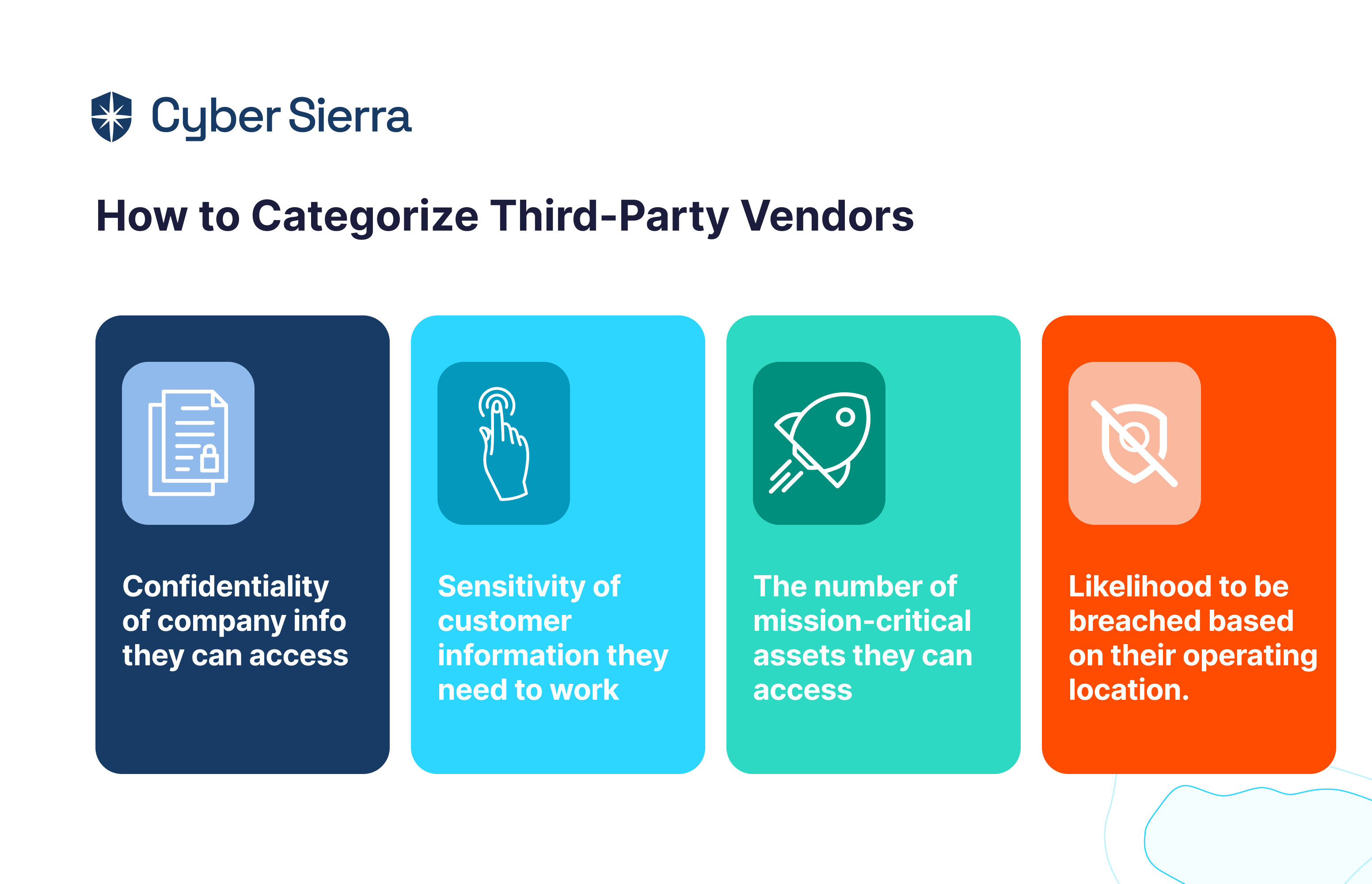
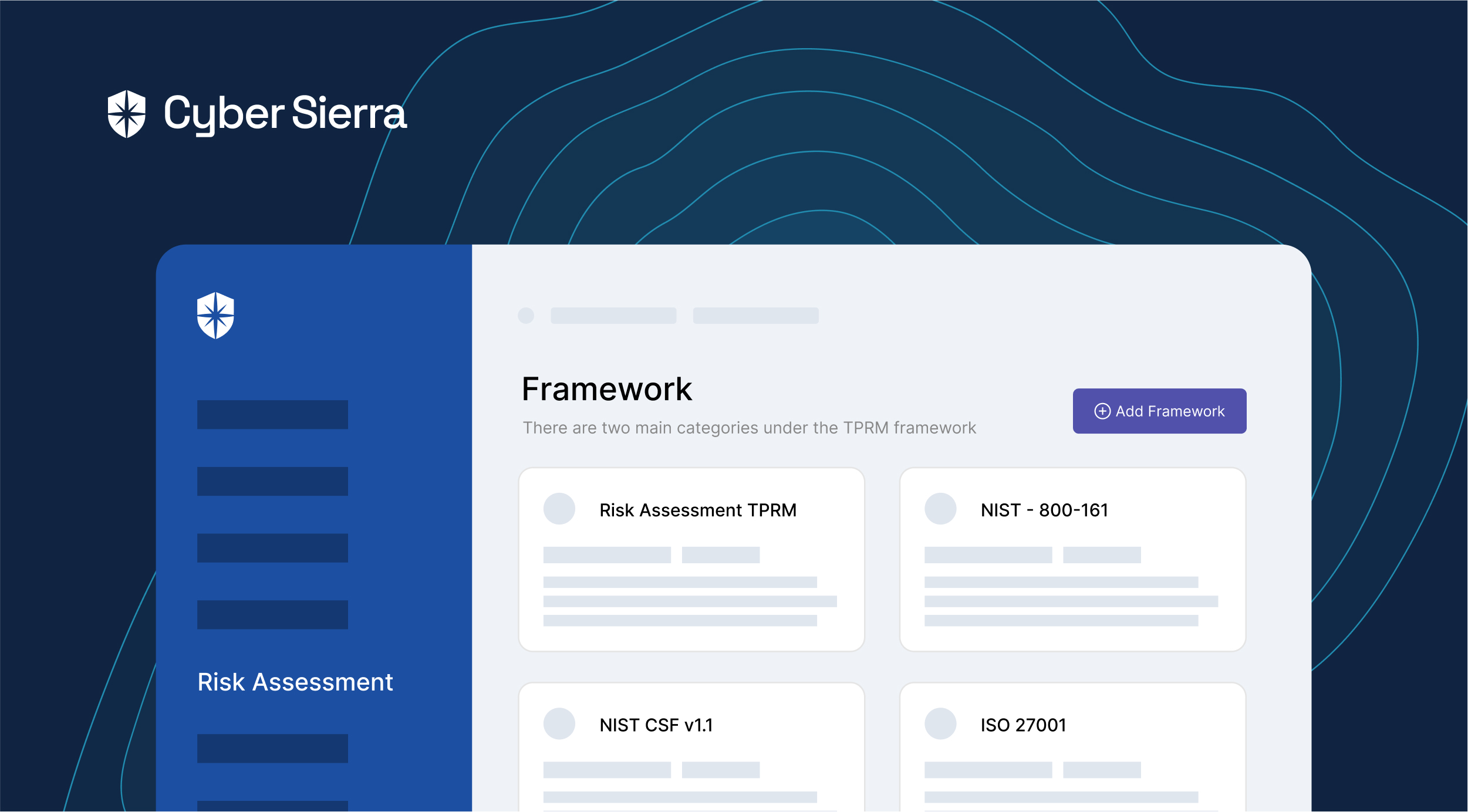
Once you’ve categorized vendors, the next step is to create, customize, and send security assessment questionnaires based on that categorization. Cyber Sierra automates this process.
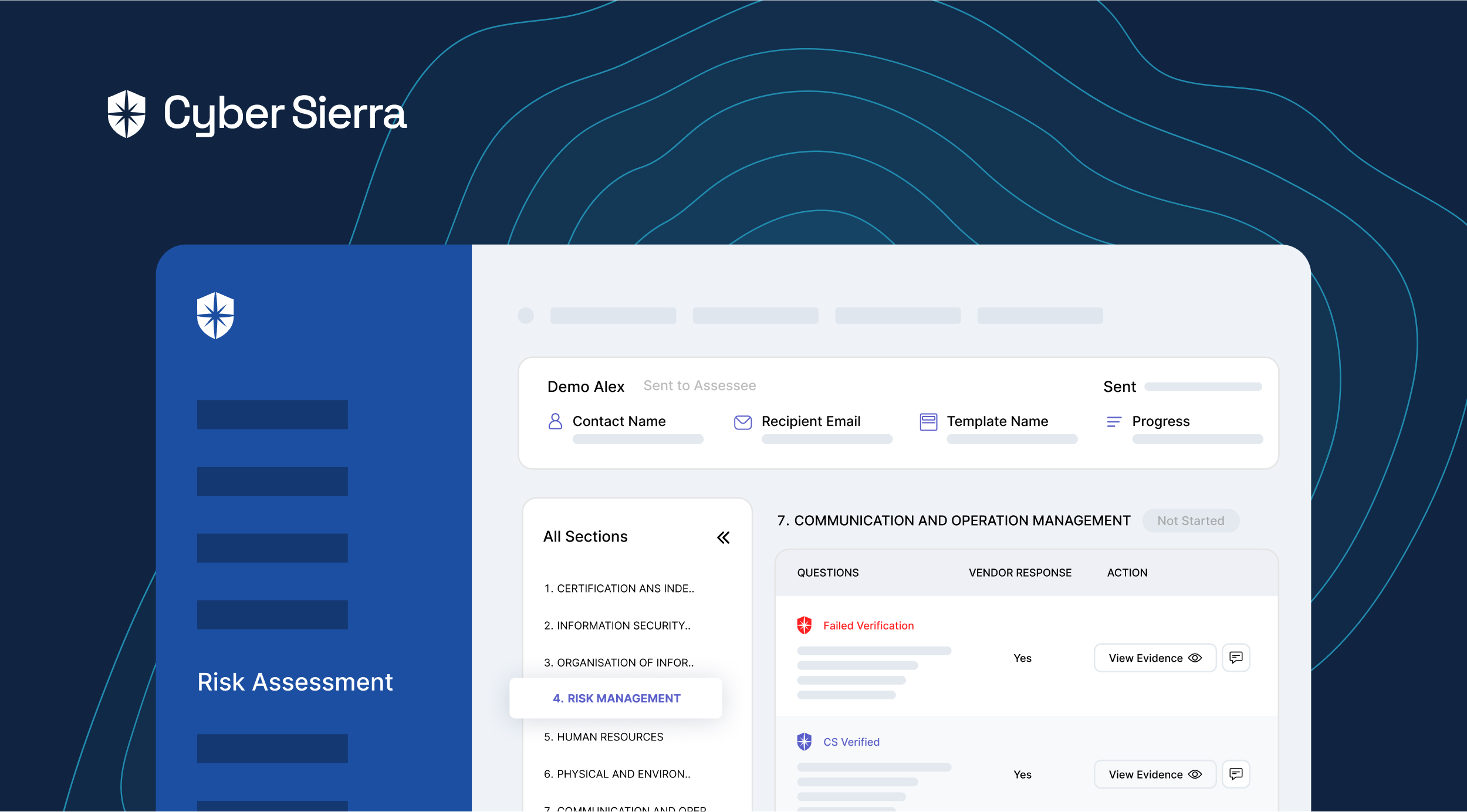
Our platform has globally-recognized vendor risk assessment templates, such as NIST and ISO. Your team can customize them to suit regional requirements for compliance programs like MAS TRM. You can also add and use your own risk assessment templates:
The steps are streamlined into:
- Choosing an appropriate assessment template
- Customizing it by selecting and editing questions needed to assess a particular third-party vendor
- Assigning reviewer(s) with different role-based access control in a few clicks, and
- Providing details of the third-party vendor such as where they are located or the assessee type they are:
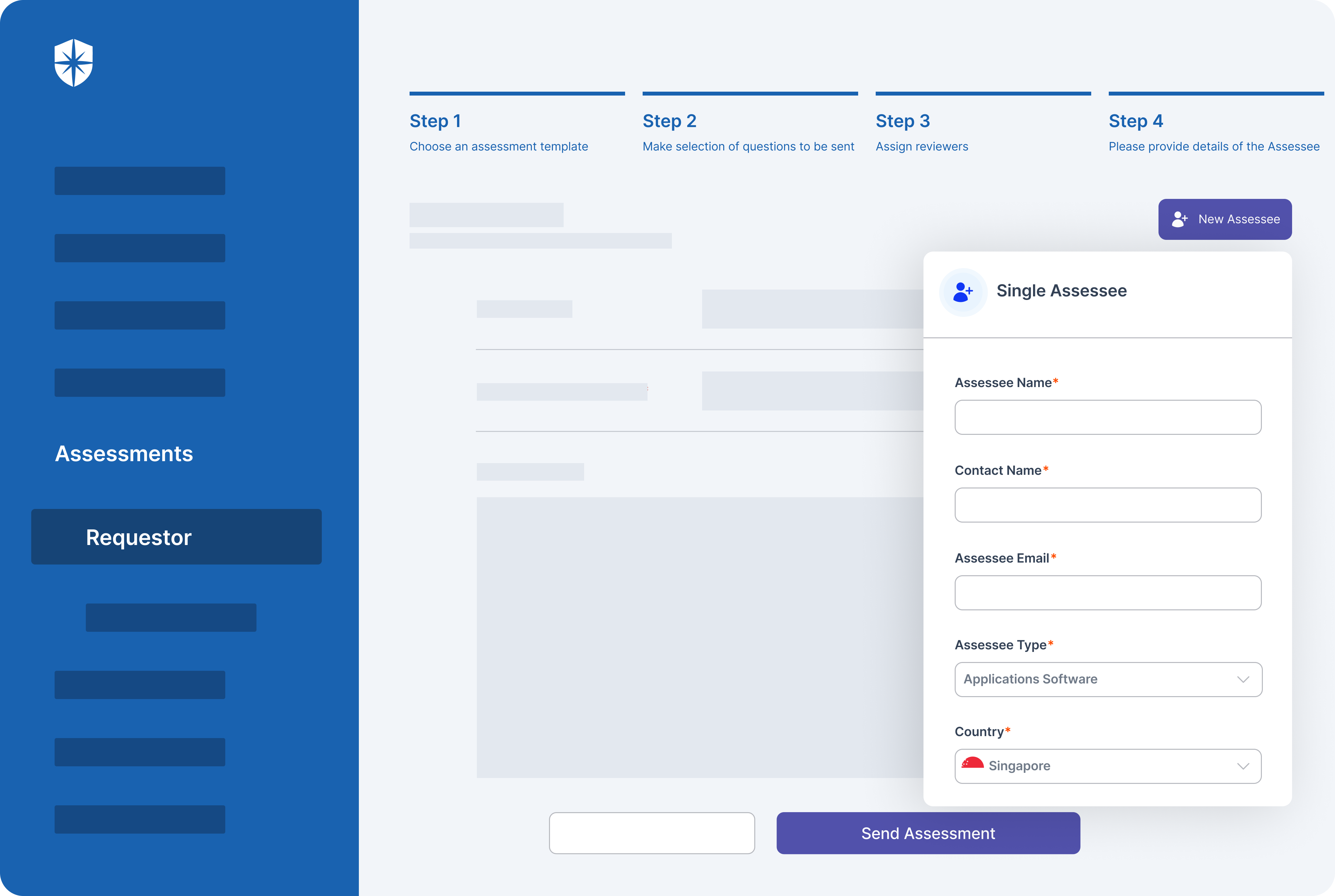
Through these steps, especially the 4th step, our platform enforces the categorization of 3rd-party vendors, right from sending out security assessment questionnaires. And by automating the entire process from one place, your organization can assess third-party risks and monitor their security postures in real-time.
That was the case for a global bank using Cyber Sierra:
Read their success story here.
Data and Operational Security Management
The last five sections of MAS TRM Guidelines deal with how organizations manage and secure data in their daily operations. Due to the dynamism involved in managing sensitive data, achieving compliance to requirements outlined in these sections calls for continuous monitoring of cybersecurity controls.
That is, your security team should:
- Continuously monitor and analyze cyber events
- Promptly detect and respond to cyber incidents.
The regulatory body recommends that:
Here’s why this recommendation is vital.
It allows enterprises to identify any changes in a provider’s risk profile over time rather than just at preset intervals, shifting from periodic risk assessments to continuous intelligence.
For instance, your organization outsources technology services to cloud providers like AWS, Azure, Google Cloud, and others. Based on the MAS TRM’s official statement, your security team should automatically, through continuous monitoring, test controls and configurations in those environments. This removes the need for manual checks and provides assurance on cloud-based controls.
Cyber Sierra automates this process:
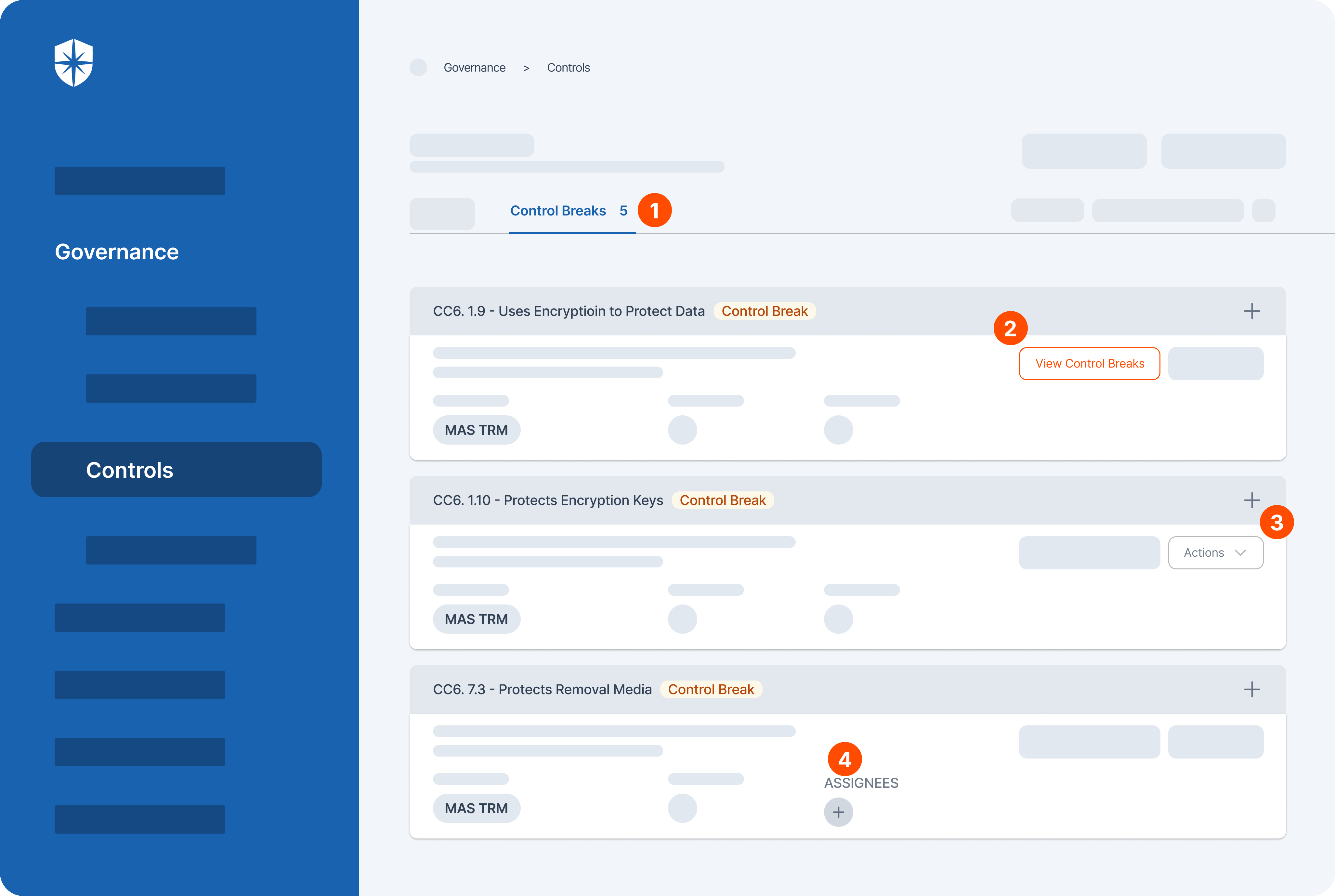
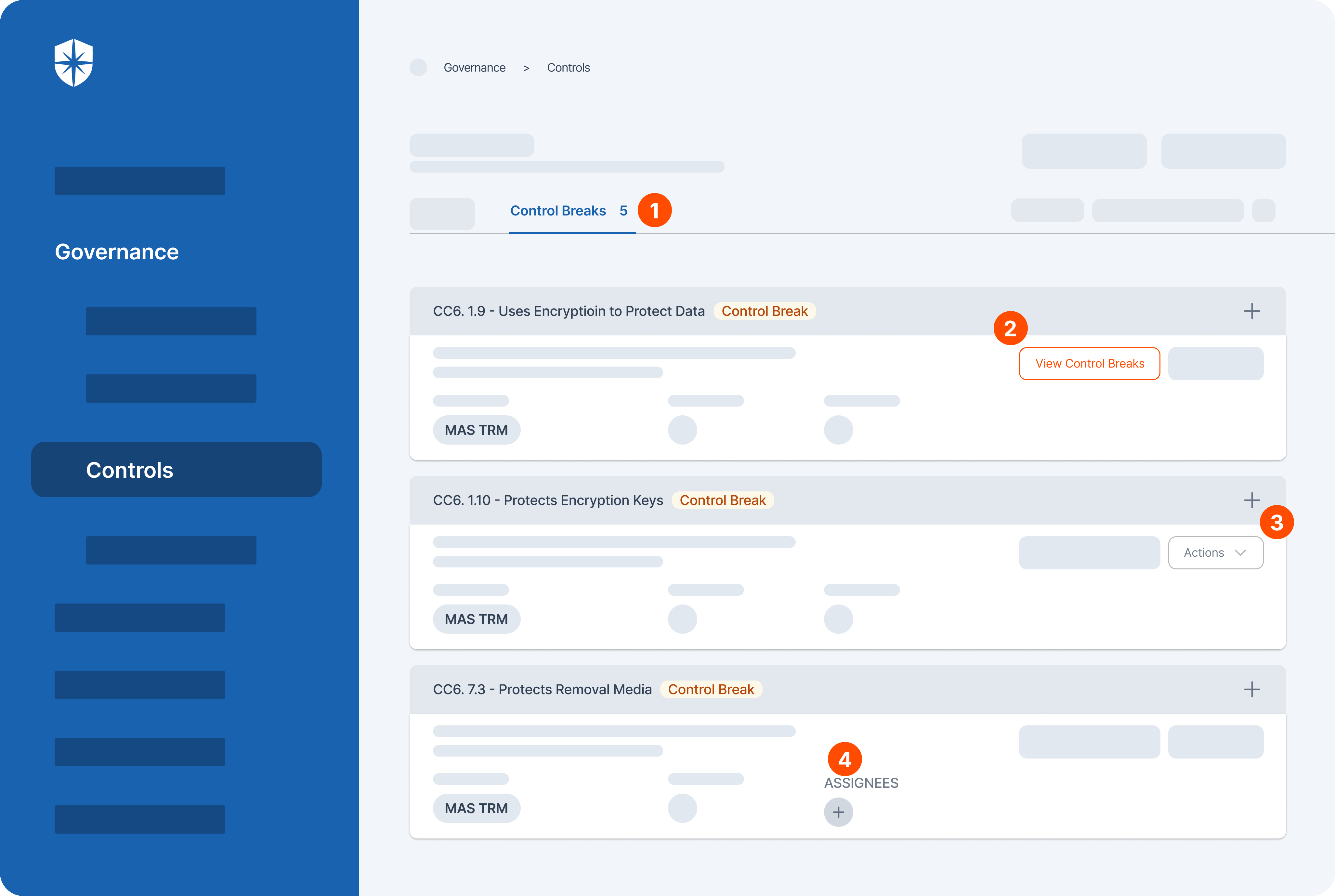
As shown, in one dashboard, your team can:
- Continuously monitor and detect MAS TRM control breaks and their corresponding vulnerabilities.
- View details of vulnerabilities related to a control break
- Get actionable tips for remediating threats, and
- Assign remediation to qualified teammates.
The Consequence of MAS TRM Noncompliance
Brand reputation damage and, of course, fines.
Those are the major consequences of violating MAS TRM Guidelines. Specific to fines, this report noted that the penalty per breach of a TRM requirement can exceed S$1 million. But it doesn’t end there. Multiple breaches of the MAS TRM requirements can result in a multi-million dollar fine for an organization.
This was demonstrated by MAS’s 2023 report of penalized financial institutions. DBS Bank was among those penalized. They were fined a whopping S$2.6 million for violations and noncompliance failures committed between July 2015 and February 2020.
Their case revealed that your organization can still be penalized several years after for noncompliance failures committed today. This necessitates the need to prioritize becoming (and staying) compliant to MAS TRM Guidelines today.
Ease through Singapore’s MAS TRM Guidelines
MAS TRM Guidelines has 15 sections.
Under each section, there are dozens of subsections of requirements organizations must adhere to become compliant. Along with these, their corresponding security controls that must be implemented. To ease the process, it is better to leverage a platform that automates most processes involved:
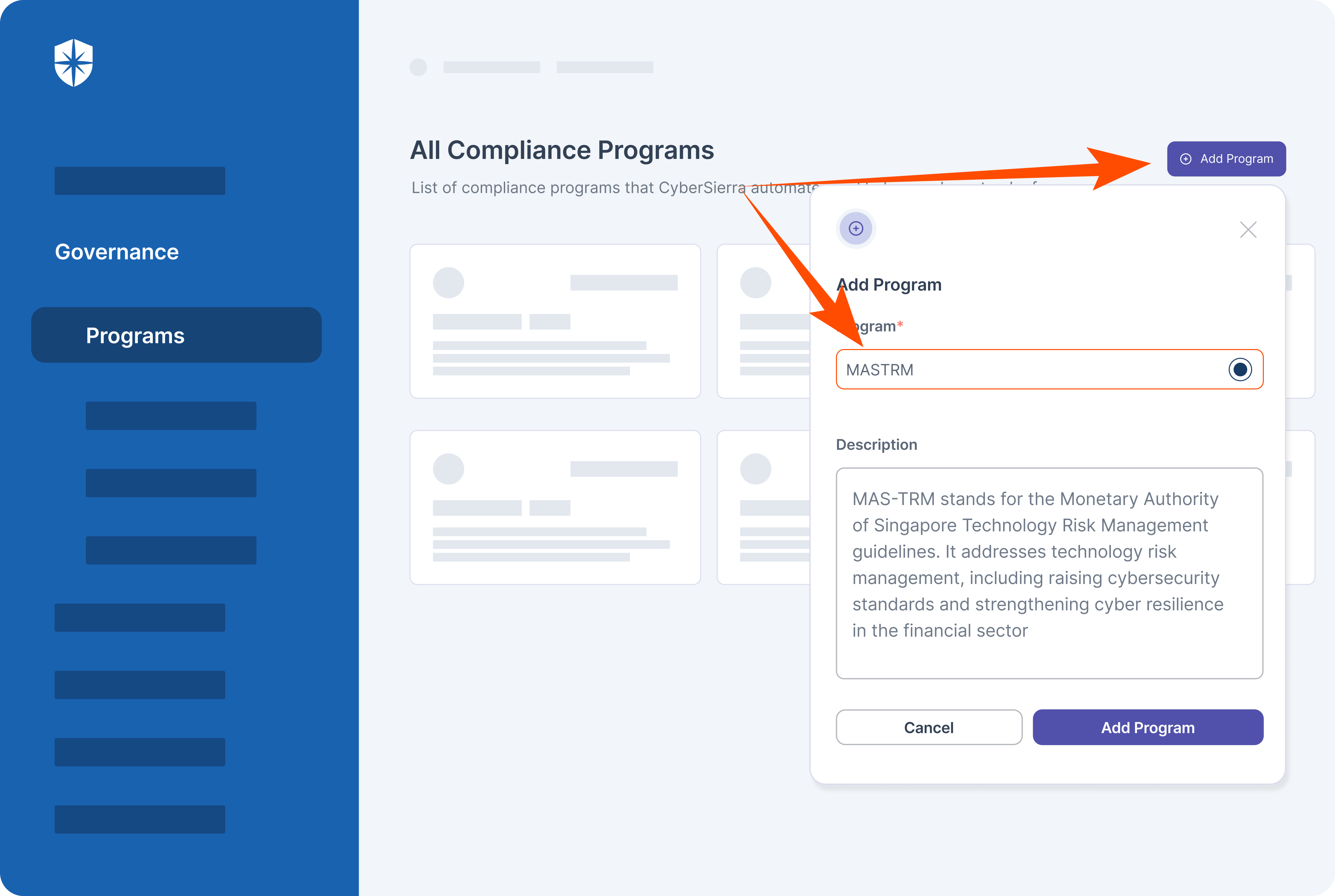
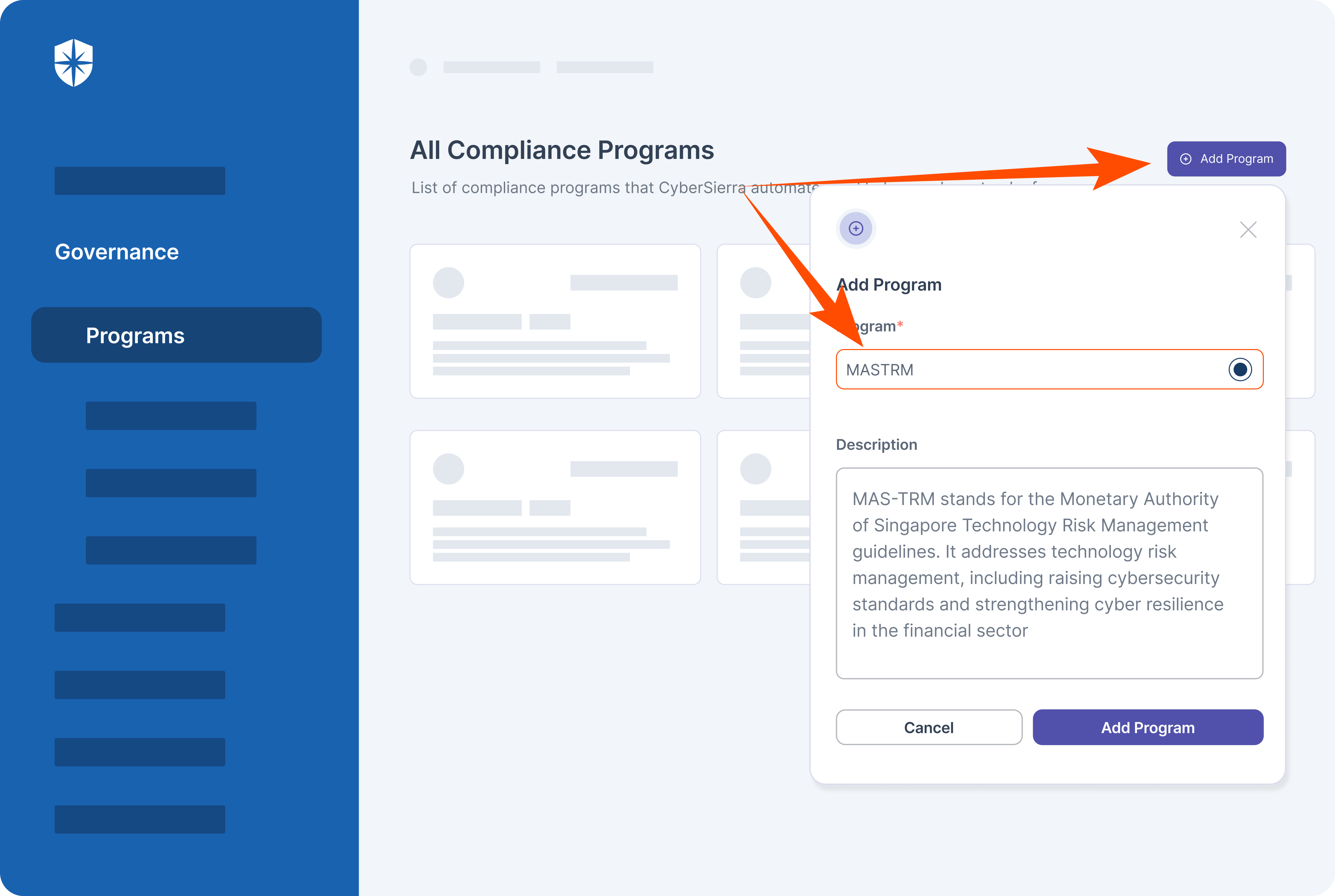
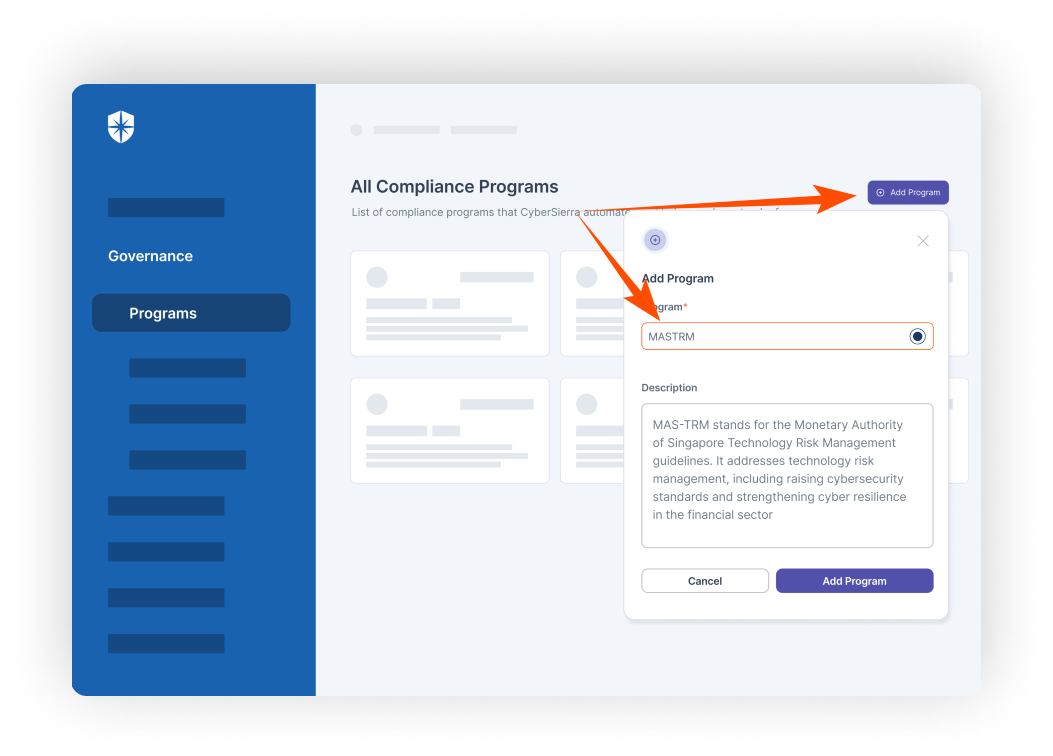
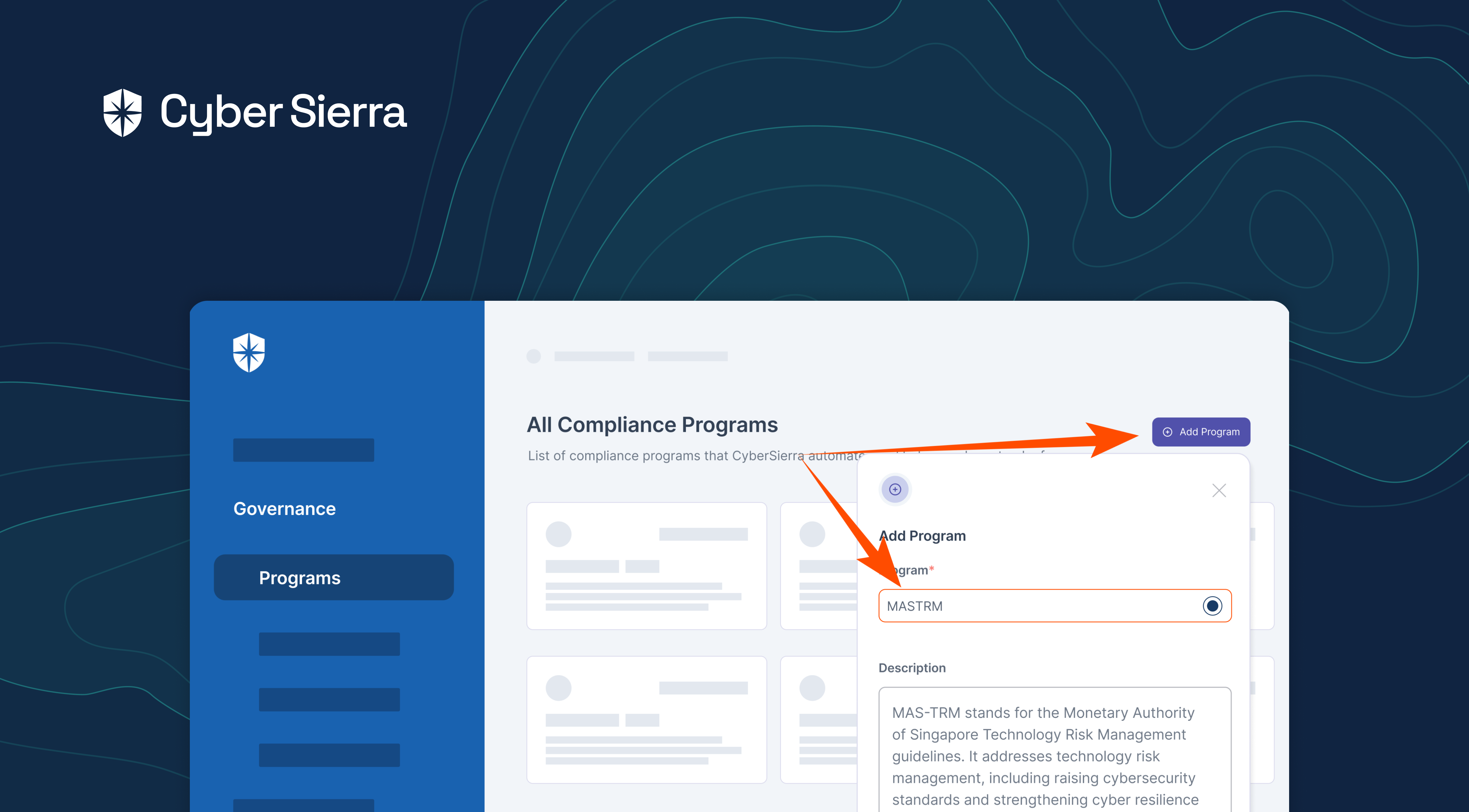
Our platform has the MAS TRM program built-in.
This means, in a few clicks, you can invite your team and work collaboratively to become (and stay) MAS TRM-compliant, while automating various tasks involved from one place.
Our platform has the MAS TRM program built-in.
This means, in a few clicks, you can invite your team and work collaboratively to become (and stay) MAS TRM-compliant, while automating various tasks involved from one place.



A weekly newsletter sharing actionable tips for CTOs & CISOs to secure their software.
Thank you for subscribing!
Please check your email to confirm your email address.
Find out how we can assist you in
completing your compliance journey.