Best Third-Party Risk Management (TPRM) Tools - Safeguarding Your Business Relationships



Join thousands of professionals and get the latest insight on Compliance & Cybersecurity.
Searching for a Third-Party Risk Management (TPRM) tool that can help manage your security posture as well as business relationships?
The market offers a myriad of TPRM tools, each promising to maintain order.
But where does one start, and how do you know which solution is the right fit for your business?
In this guide, we’ll break it down for you. We’ll explain the nuances of TPRM and how it can effectively oversee your business relationships.
We’ll also give you some pointers on choosing the right TPRM tool for your business so you can start managing risks today!
Let’s get started.
What is Third-Party Risk Management (TPRM)?
Third-party risk management (TPRM) is a process that helps organizations identify, assess, and manage risks associated with their business relationships with third-parties. This includes the vendors, contractors, suppliers, distributors, and other parties that you work with to grow your business.
TPRM is an important part of enterprise risk management, and helps identify and manage risks associated with business operations. Third-party risk management tools can help enterprises analyze, assess, and manage these risks.
Your organization can also use TPRM tools to minimize legal liability and financial loss risks. It’s a crucial part of any security program that aims to prevent data breaches, cyber-attacks, and other threats related to information security.
Why Do You Need Third-Party Risk Management Tools?
TPRM tools extend beyond risk assessment and monitoring. They provide a comprehensive, data-driven framework for risk management, while also automating processes. This automation not only reduces the likelihood of human errors but also greatly expedites operational workflows.


Here are some essential reasons why you should use third-party risk management tools:
1. Assessing and Monitoring Risks
Third-party risk management tools play a pivotal role in evaluating and overseeing risks that can stem from diverse origins, including legal obligations, operational interruptions, and cyber vulnerabilities.
In the Gartner survey of 100 executive risk committee members in September 2022, 84% said third-party risks resulted in disruptions in operations.
A ‘miss’ occurs when a third-party risk incident results in at least one of the outcomes as shown below.
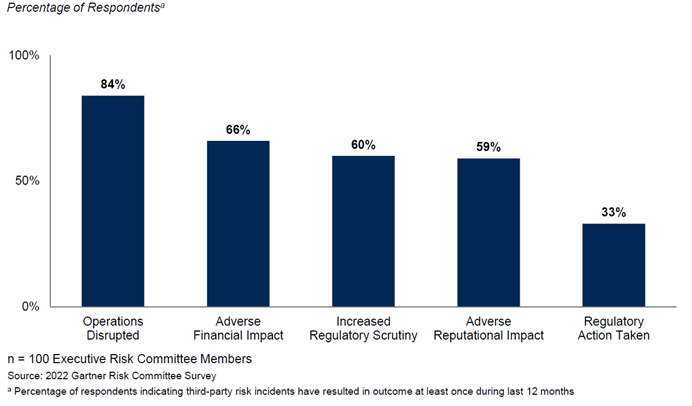
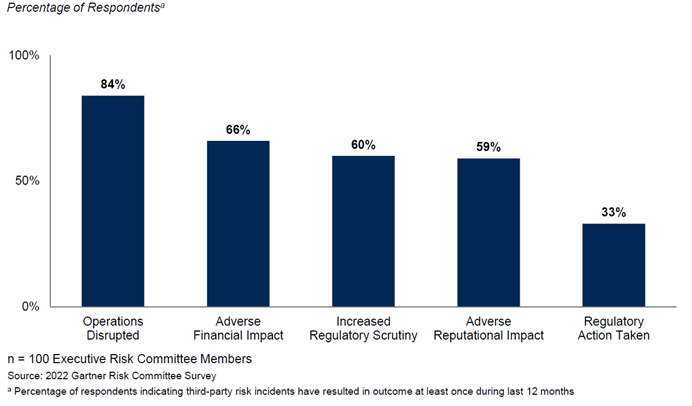
This shows how organizations that adopt third-party risk management tools can better assess, monitor, and manage their risks.
2. Automation and Efficiency
The automation provided by TPRM tools can
- Save valuable resources,
- Reduce human error, and
- Accelerate operations.
Automation offers a more uniform approach to managing third-party risks by eliminating individual biases and ensuring all third parties are scrutinized to the same degree.
3. Complexity in Supply Chain Processes
The increased reliance on third-party vendors and global sourcing has added multiple layers of complexity to the supply chain.
As a result, it has become difficult for businesses to manage the associated risks without the assistance of TPRM tools.
A 2023 report from KPMG revealed that 82% of businesses faced a supply chain disruption due to third-party risk, emphasizing the importance of TPRM tools.
4. Regulatory Compliance
Heightened regulatory requirements mandate companies to manage third-party risks effectively. TPRM tools can help businesses achieve regulatory compliance by providing clear visibility into the third-party risk landscape.
Key Considerations for Choosing TPRM Tools
Selecting the optimum Third-Party Risk Management (TPRM) tool isn’t a task one should take lightly.
Multiple vital aspects must be considered to ensure the tool aligns well with your business dynamics while offering substantial value in risk management.
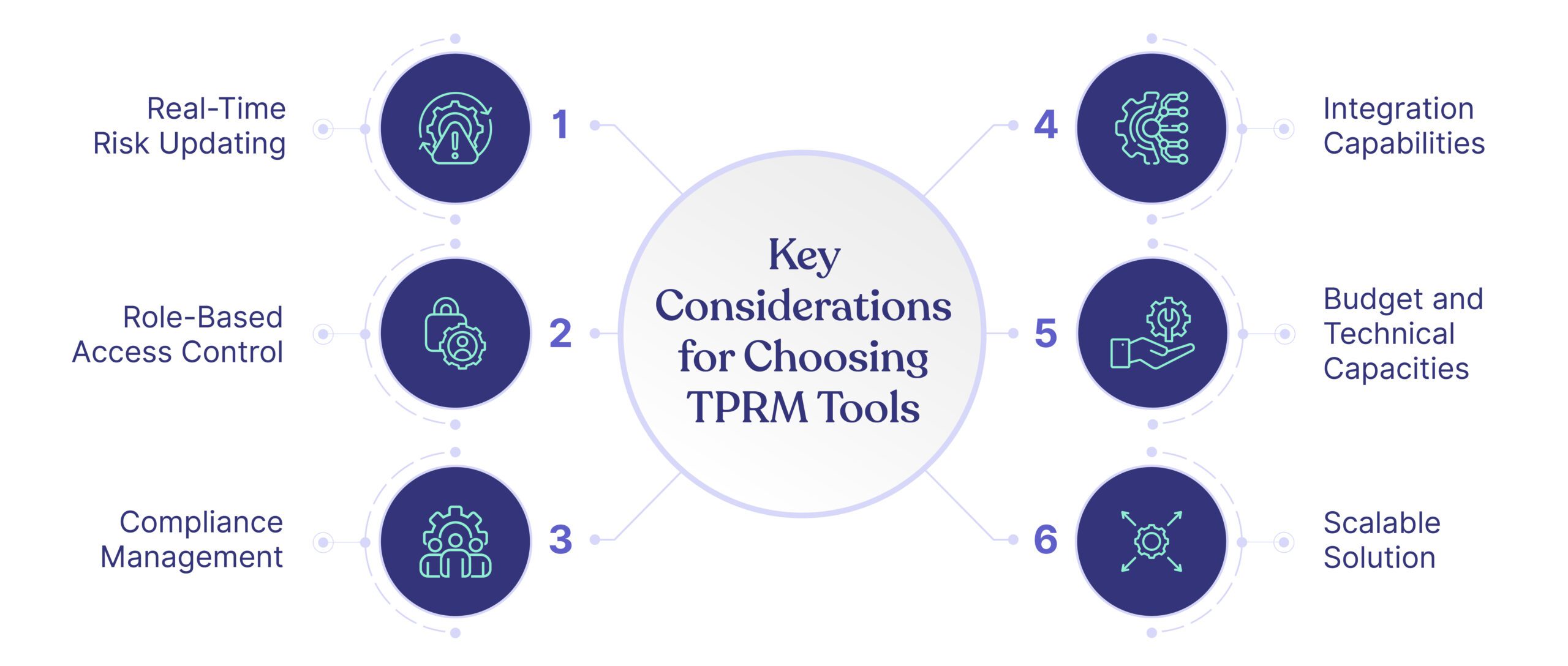
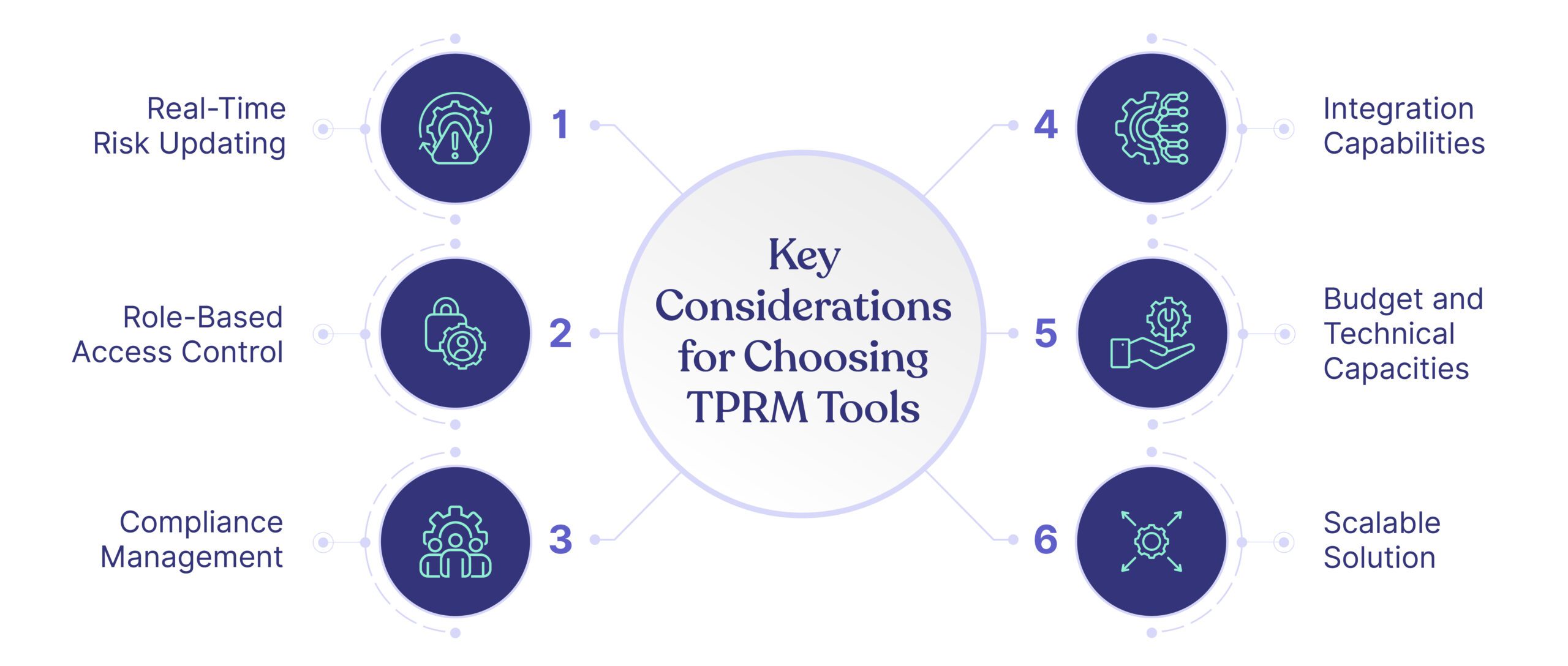
These include:
1. Real-Time Risk Updating
Consider a sudden data breach at a third-party vendor; how promptly would you know?
Risks can emerge in the blink of an eye. Quick visibility into such risks is crucial.
Thus, a TPRM tool should be able to update risk assessments in real time, providing immediate visibility into vulnerabilities.
Such a feature enables businesses to respond promptly and effectively to emerging threats and manage their third-party risks proactively.
2. Role-Based Access Control
What would happen if sensitive data falls into the wrong hands within your own organization due to loosely controlled access rights? Preventing such scenarios is where role-based access control becomes invaluable.
Role-based access control is a vital feature in a TPRM tool and allows you to assign specific access privileges based on user roles and control permissions. Doing this ensures that critical information is only accessible to those needing it, enhancing data security and reducing the chance of internal data breaches.
3. Compliance Management
The terrain of regulatory compliance is increasingly complex and dynamic. Companies are expected to keep pace with constantly evolving local and global standards, which can result in costly penalties or irreparable reputational damage. This is where having a TPRM tool with a robust compliance management feature becomes pivotal.
A robust TPRM tool should equip the enterprise to respond to compliance requirements and manage compliance as an ongoing initiative, aligning with local and global regulations.
Whether it’s GDPR for data protection, SOC2 for service organizations, or ISO27001 for information security management, your TPRM tool should be capable of managing compliance with these diverse standards.
The tool should employ measures to track your company’s compliance status regularly, issuing reminders for mandatory assessments, audits, or reporting.
4. Integration Capabilities
Integration capabilities ensure the tool synergizes well with your existing systems. A TPRM tool that integrates smoothly with other platforms (such as your CRM, ERP, or ITSM) enhances data-sharing, process synchronization, and overall operational efficiency.
5. Budget and Technical Capacities
Lastly, businesses must strike a balance between the offered features and the cost of the TPRM tool. Evaluate if the tool provides good value for the price and aligns with your budgetary constraints.
At the same time, assess your team’s technical prowess and readiness to implement and use the tool to its fullest. You should also look for a tool that offers employee training and support, as this reduces the overall learning curve.
6. Scalable solution
Look for a TPRM tool that is scalable and can accommodate your organization’s growth, increasing vendor relationships, and expanding risk landscape. This flexibility ensures that the TPRM tool remains effective and relevant as your business continues to flourish.
Top Third-Party Risk Management Tools for 2023
Numerous quality tools are available for Third-Party Risk Management. Based on the functionality, user reviews, and reputation within the industry, the top contenders for 2023 are:
- Cyber Sierra
- BitSight
- One Trust
- Upguard
- Venminder
Let’s look at the details of the tool one by one:
1. Cyber Sierra
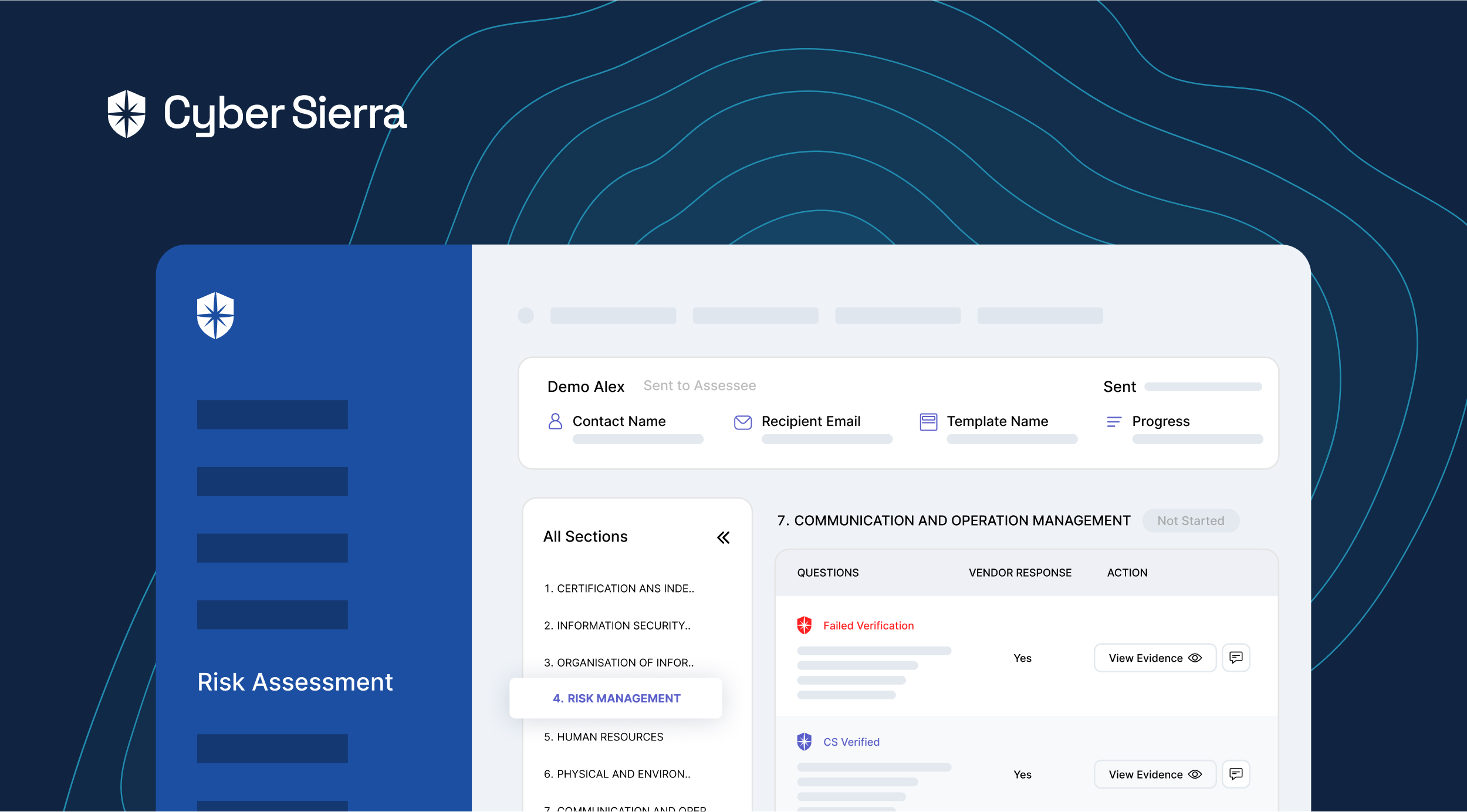
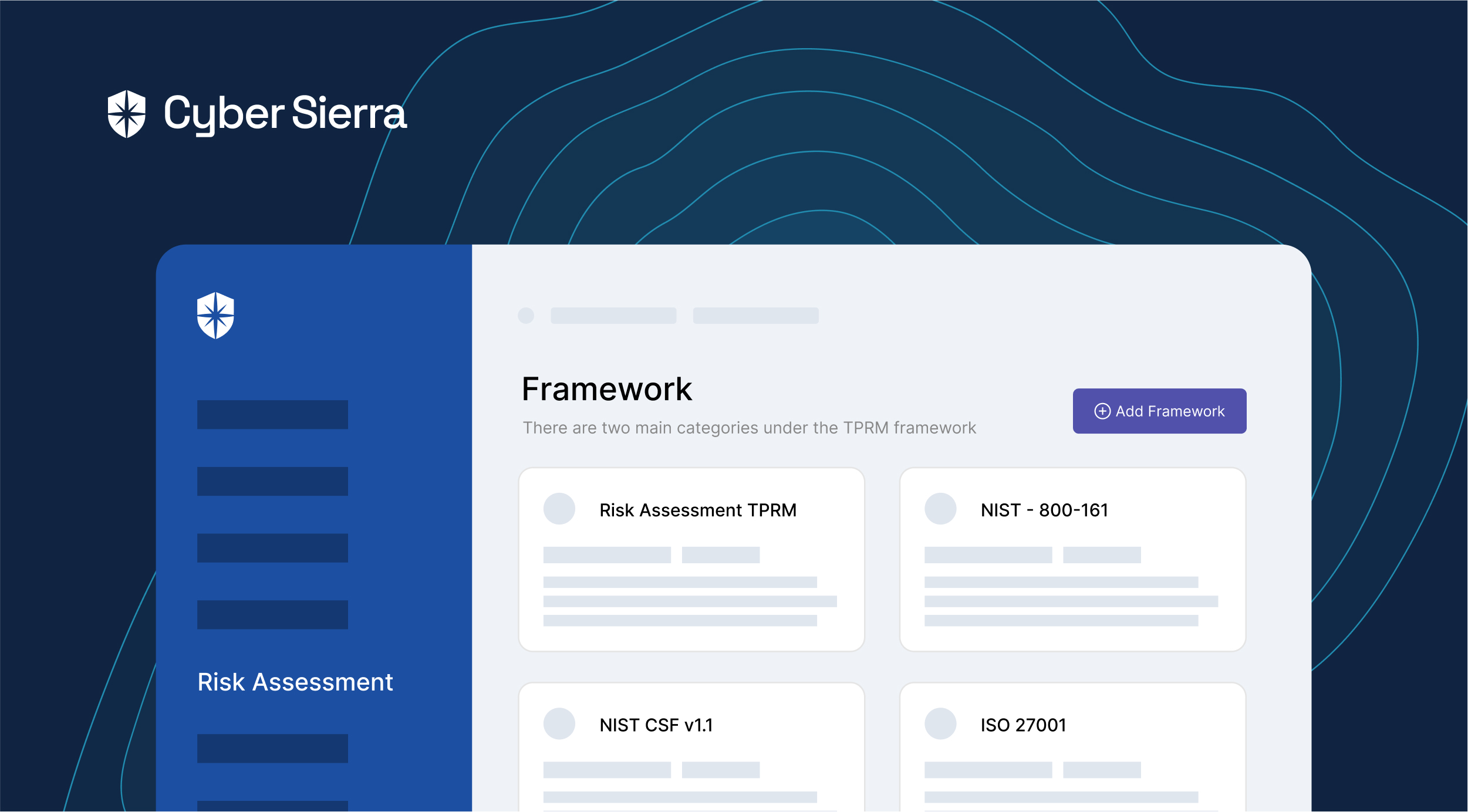
Cyber Sierra TPRM program empowers enterprises to evaluate, mitigate, and monitor third-party vendor risks.
Here are the key features of Cyber Sierra:
- Identify third-party risks: Gain insight into the key risks associated with third-party vendors and develop an understanding of how to identify them
- Remediate & manage vendor risks: Implement a structured framework to evaluate, assess, and automate your third-party risk management processes
- Prioritize your vendor inventory: Categorize vendors by risk level to allocate resources efficiently and prioritize high-risk vendors for focused attention
- Continuously monitor all your vendors: Get near real-time 24*7 visibility of all your vendors’ security compliance with alerts and correction actions on a need basis
These key features are built around being proactive in threat detection and swiftly managing risks to provide organizations with an efficient and robust solution.
Cyber Sierra’s TPRM program is customizable to the needs of different industries and ensures compliance with region-specific regulations, such as Singapore’s PDPA, Australia’s CIRMP, Europe’s GDPR, and USA’s CCPA, HIPAA, and PCI DSS, to name a few.
It also comes with a training module to equip employees with awareness on various security topics.
What’s good: Cyber Sierra stands out for its vendor risk assessment and due diligence, intuitive interface, and powerful risk management and reporting.
2. BitSight
BitSight specializes in security ratings and risk management. Its features include automated risk prioritization, detailed analytics, and robust third-party risk management capabilities.
Here are the key features of BitSight:
- Security Ratings: Get objective and quantifiable measurements for your cybersecurity posture and vendors.
- Atlas Platform: Get a user-friendly 360-degree risk view, enabling risk segmentation and peer comparison.
- Peer Benchmarking: Benchmark your organization and vendors against industry peers.
This gives you a broad perspective of your organization’s risk landscape, enabling you to effectively understand and prioritize your risk mitigation efforts.
What’s good: BitSight’s strength lies in its detailed risk assessments, comprehensive security ratings, and ability to simplify complex data points into actionable insights.
3. OneTrust Third-Party Risk Management
OneTrust TPRM is a part of OneTrust’s larger privacy, information security, and governance platform, facilitating a holistic approach to risk management. Some notable features are its automation capabilities, central repository for third-party data, and risk identification tools.
Here are the top features of OneTrust TPRM:
- Unified Privacy, Governance, and Risk Platform: Access a comprehensive platform that covers privacy, information security, and governance.
- AI-Powered Risk Analysis: Employ artificial intelligence for identifying and prioritizing relevant risks.
- Scope Wizard: Automatically determine which assessments to perform on each vendor based on collected information.
What’s good: OneTrust integrates smoothly with various management systems, ensuring consistency in data collection, analysis, and reporting. It also helps streamline vendor assessments with its automation features.
4. UpGuard
UpGuard combines a comprehensive solution with third-party risk management, security posture management, and data leak detection. It provides scores to indicate the cybersecurity risk level of vendors and helps maintain continual visibility and control over data.
Here are the top features of UpGuard:
- Continuous Assessment: Get real-time updates on your vendors’ cyber risks, enabling your organization to react promptly to emerging or changing risks.
- BreachSight: Proactively detect data leaks or exposed credentials to prevent severe data breaches, protecting your company’s reputation and finances.
- Actionable Remediation Guidance: Get specific guidance to quickly and effectively rectify identified security issues, enhancing your overall cybersecurity posture.
What’s good: UpGuard has a robust risk scoring system, ability to discover and remediate data leaks, and offers consistent monitoring of every vendor.
5. Venminder
Venminder offers a robust TPRM solution with services including contract management, due diligence and risk assessments, questionnaires, and ongoing monitoring capabilities. You can store all third-party risk data and information in one place, simplifying audits and reporting.
Here are the top features of Venminder:
- Managed Services: Reduce your internal team’s workload, allowing them to focus on core business tasks.
- Third-Party Expert Evaluations: Get expert evaluations that provide reliable and accurate assessments to help you make informed and confident decisions about your vendors.
- Regulatory Compliance Focus: Ensure your vendor relationships meet regulatory standards to avoid fines and other negative consequences of non-compliance.
What’s good: Venminder’s focus on ongoing monitoring and its excellent regulatory compliance capabilities, which can be essential for businesses in regulated industries.
How TPRM Tools Improve Vendor Performance Monitoring?
TPRM tools play a pivotal role in enhancing the monitoring of vendor performance through a multitude of key mechanisms.


1. Centralized View
TPRM tools consolidate and present your vendor data within a single centralized platform. This capability fosters a more streamlined and effective approach to vendor management. The integration of all data into one location guarantees your continuous awareness of any alterations or potential risks linked to your vendors.
Consider this scenario: if a vendor displays early indications of a potential data breach, a TPRM tool would promptly notify you, enabling swift and decisive responses.
Likewise, instances of vendors consistently falling short of performance benchmarks become readily identifiable and manageable through this centralized viewpoint.
2. Standardizing Performance Metrics
TPRM tools provide standardized metrics to track vendor performance. Standardization can reduce confusion and miscommunication, as everyone involved clearly understands the benchmarks for performance.
You could establish Key Performance Indicators (KPIs) such as quality of service, delivery time, data security standards, or anything relevant to your business that a vendor needs to deliver on.
The ability to easily track these KPIs over time helps compare vendors and choose who should continue being part of your business based on their consistent performance.
3. Actionable Insights
TPRM tools often provide advanced analytics and reporting functionality. This enables you to carry out deeper analysis and gain valuable insights into your vendors’ overall performance and the risks they pose.
They can highlight patterns and trends that may be less visible in day-to-day operations. Consequently, these insights allow you to move from reactive to proactive – you don’t need to wait for problems to occur but stop them before they happen.
These insights can also guide decision-making processes for contract renewals, renegotiations, and vendor selection.
4. Vendor Sourcing and Onboarding
Some TPRM tools offer unique features to help with vendor sourcing, selection, and onboarding. They may come with capabilities to perform an initial assessment of potential vendors, ranking them based on the organization’s specific needs and requirements.
This ensures a smooth and systematic onboarding process and sets the tone for what is expected from vendors.
It helps kick-start the vendor’s journey on the right foot — knowing exactly what performance metrics they’ll be judged upon, minimizing future surprises, and ensuring optimal performance.
Over time, this can transform your relationships with your vendors, resulting in better collaboration and performance.
Enhancing Vendor Due Diligence with TPRM Tools
Vendor due diligence is a critical aspect of the procurement process. TPRM tools help to automate, streamline, and improve this process by providing rigorous risk assessment protocols, tracking vendor interaction, and providing real-time insights to make informed decisions.
The right TPRM tool will enhance your performance, minimize risks, and help maintain successful and secure business relationships.
Though all the tools can help you with vendor due diligence, the one that is best for your organization will depend on your business needs and the type of procurement processes you have. Look for solutions that meet your current and future needs.
Cyber Sierra, for instance, grants you much more than an ordinary TPRM solution. Its comprehensive suite leapfrogs the limitations of conventional point solutions by offering a platform with a unified cybersecurity approach. With Cyber Sierra, you also get:
- Regular security awareness training for employees,
- Compliance with the dynamic regulatory landscape,
- Prompt resolution of cloud misconfigurations,
- Simplified management and renewal of cyber insurance policies.
Book a demo and see how the Cyber Sierra’s platform can help you stay ahead of the curve and manage your risk more efficiently.



A weekly newsletter sharing actionable tips for CTOs & CISOs to secure their software.
Thank you for subscribing!
Please check your email to confirm your email address.
Find out how we can assist you in
completing your compliance journey.