Enterprise Cybersecurity Continuous Control Monitoring Examples



Join thousands of professionals and get the latest insight on Compliance & Cybersecurity.
Examples of using cybersecurity continuous control monitoring (CCM) for enterprises revolve around three core areas:
- Compliance automation
- Cyber threats’ remediation
- Vendor risk management.
Across these core areas, lots of activities go into implementing an effective cybersecurity CCM program. This piece will discuss examples in these areas. You’ll also see how enterprise security teams simplify implementation processes with a cybersecurity CCM tool.
Before we get to those…
Why Is Cybersecurity Continuous Monitoring Important?
Two main reasons:
- You get real-time visibility into your company’s internal controls and cybersecurity infrastructure for taking timely security actions.
- It increases your security team’s productivity.
Gartner’s research corroborates:
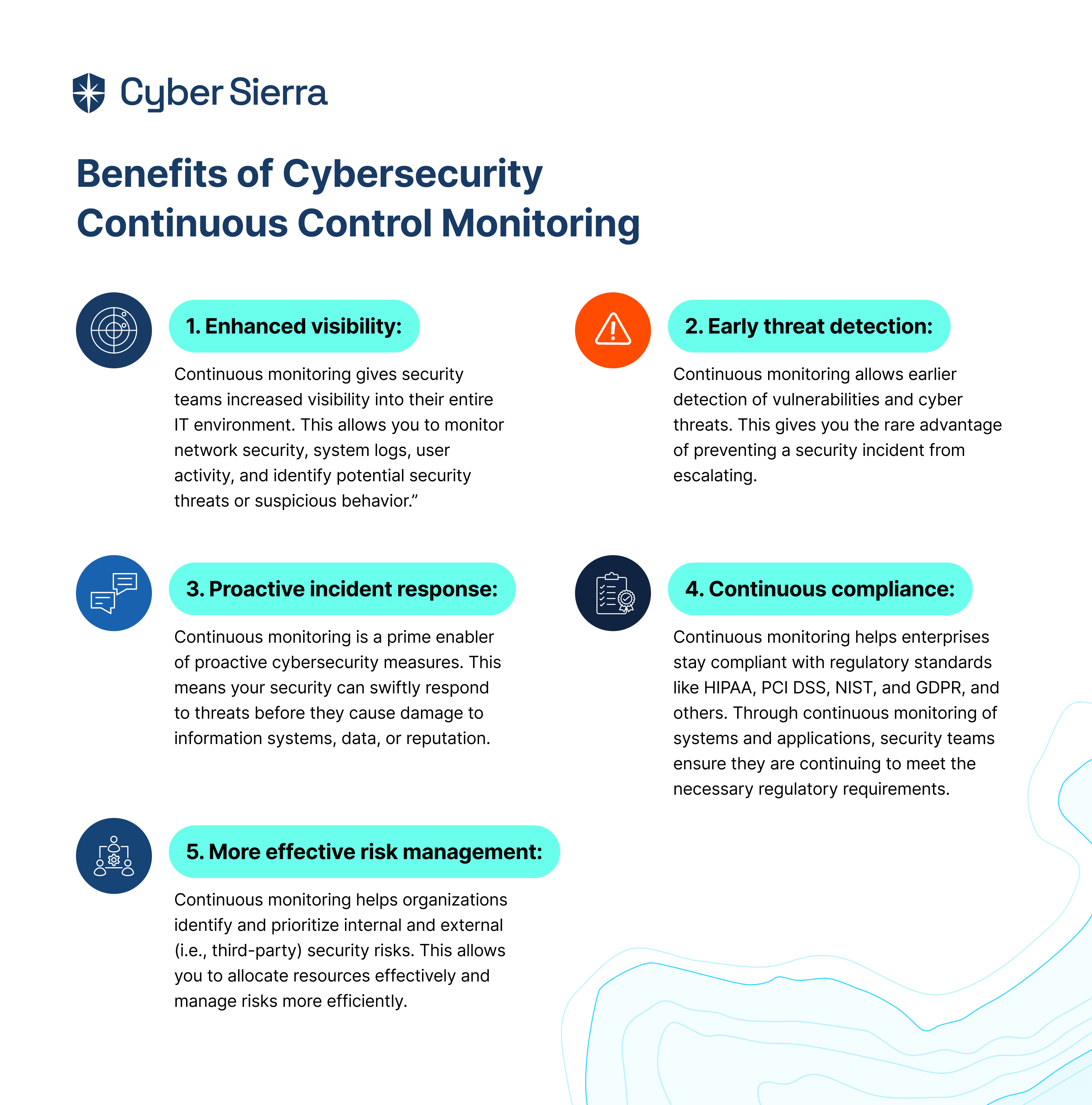
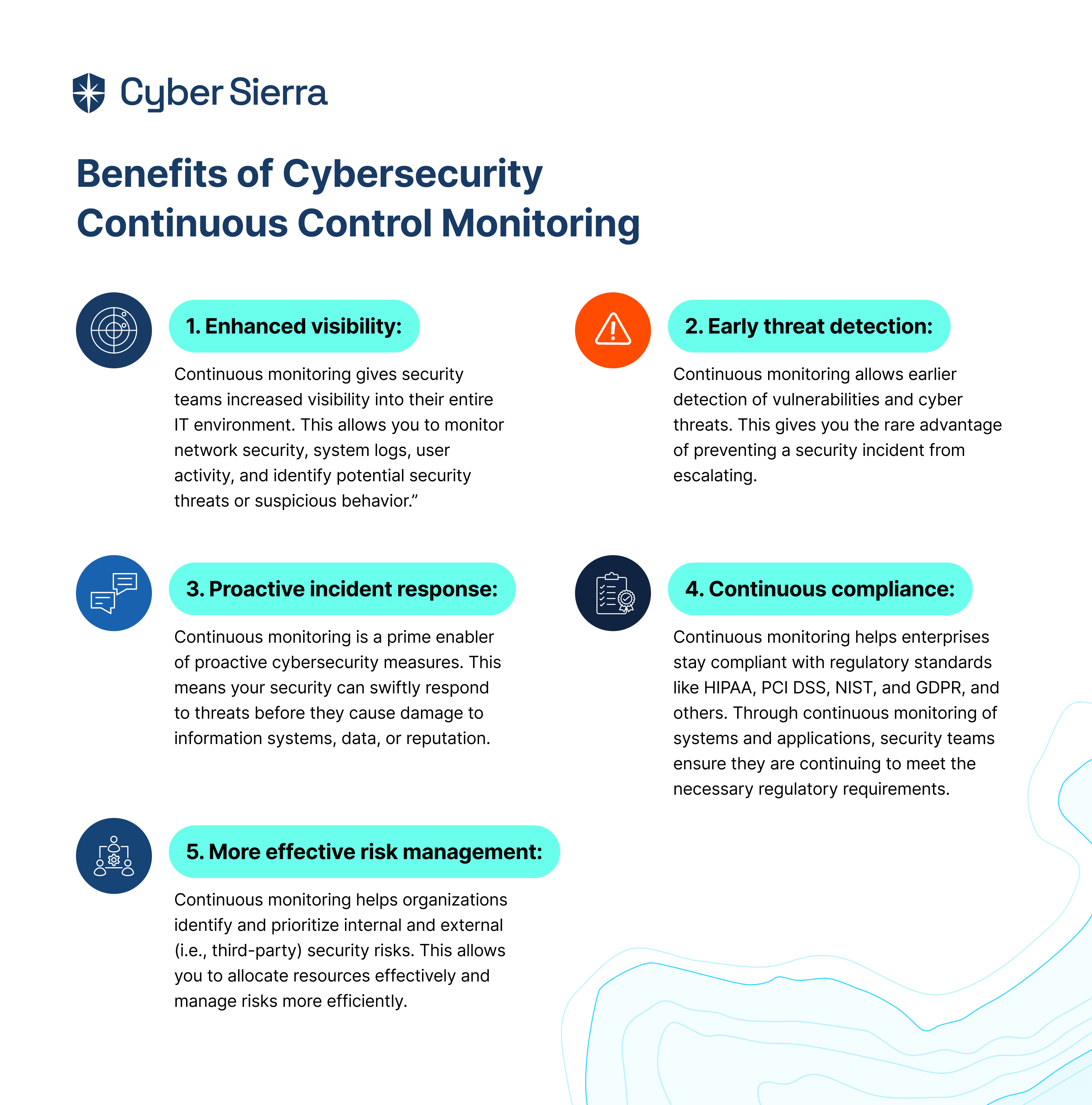
Beyond its importance, if implemented properly, the benefits of CCM are enormous. Chief Information Security Officers (CISOs) and enterprise tech execs leverage it to unlock benefits such as:
- Enhanced visibility
- Early threat detection
- Proactive incident response
- Continuous compliance, and
- More effective risk management:
But there’s a caveat.
It’s difficult, if not impossible, to attain these benefits without properly implementing cybersecurity CCM. And that’s because continuous control monitoring has a whopping seven (7) lifecycle implementation phases:
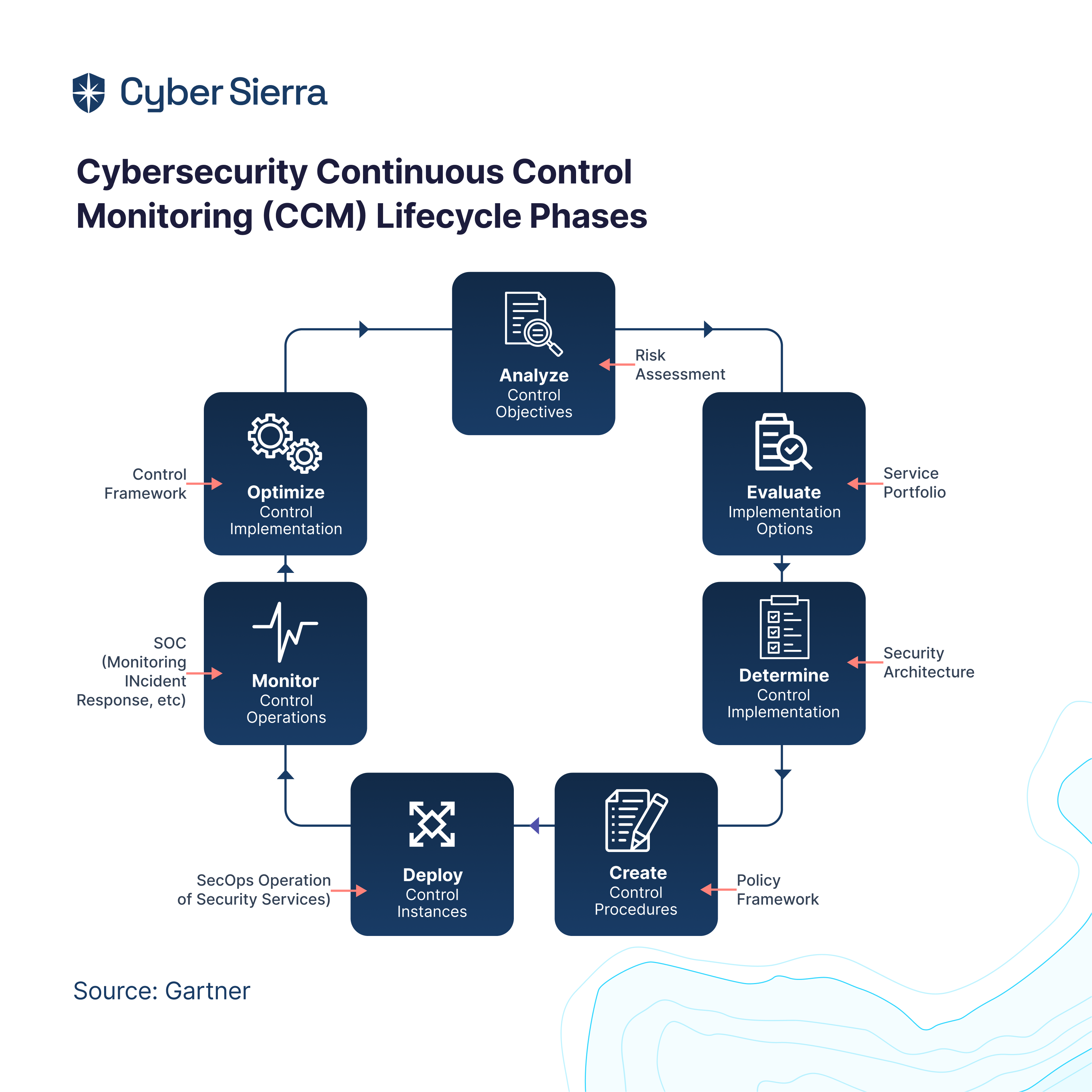
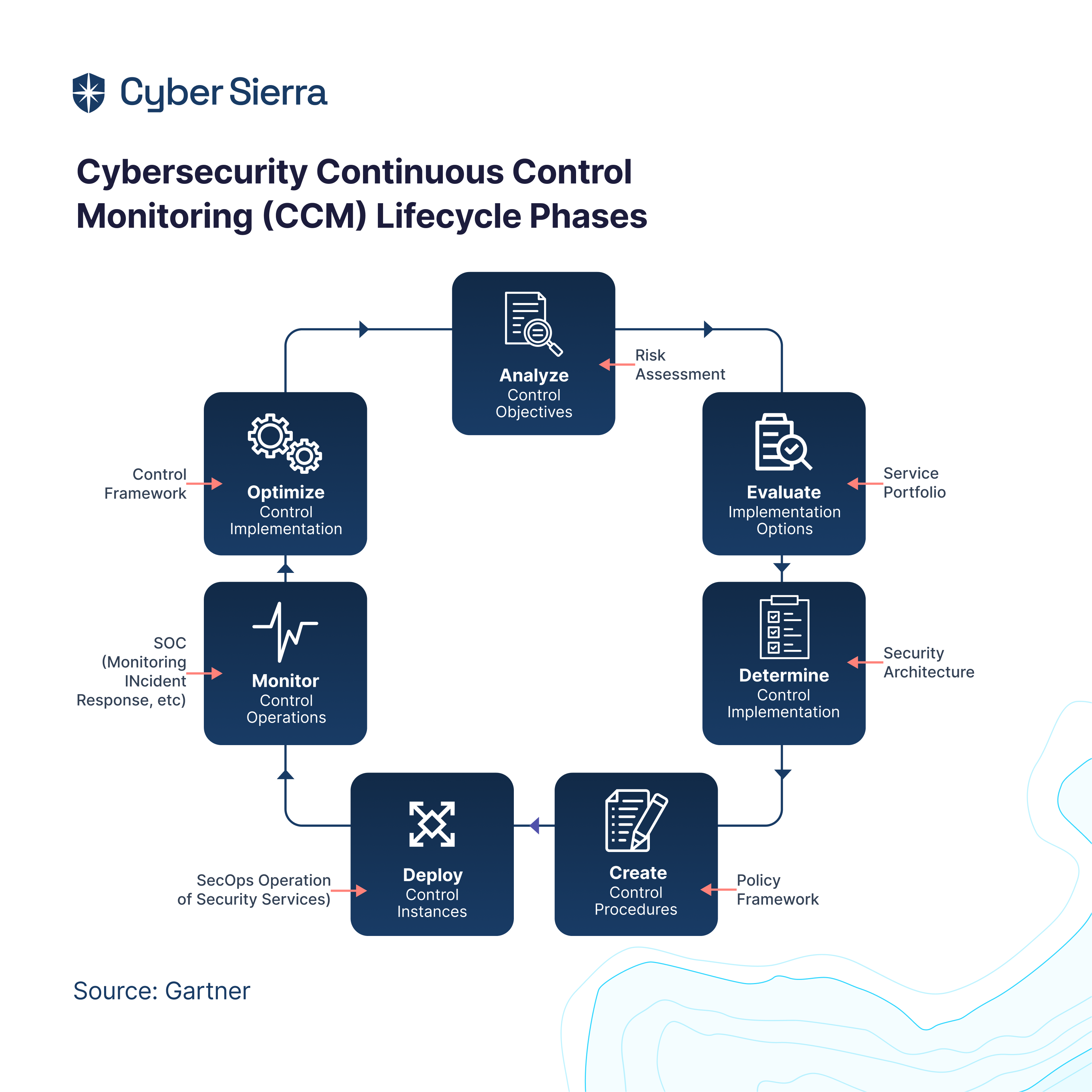
If you’re just getting started, knowing this is crucial before trying to replicate examples. To help you, we created this cybersecurity CCM checklist relied on by enterprise CISOs and tech execs.
Grab a free copy below. It’d help your security team implement CCM properly, as you aim to replicate the examples that follow:
Enterprise Examples of Continuous Control Monitoring
Gartner notes that:
The highlight above brings us to the first example (and prominent use case) of continuous control monitoring in cybersecurity:
1. Compliance Automation
There are numerous privacy laws and regulatory frameworks enterprise orgs must be compliant with today. From global programs such as SOC 2 Control , GDPR, ISO 27001, to local ones like CCPA in California or Singapore’s Cyber Essentials Mark, the list goes on.
Here’s the most challenging part.
Each of these frameworks, whether global or local, has dozens of mandatory security controls. Ensuring each control is working as required by policy, as Gartner notes, is the only way a company remains compliant. And to achieve this, automating the entire compliance processes across all programs is necessary.
That’s a perfect example (and use case) of continuous, automated monitoring of compliance controls. With a pure-play cybersecurity CCM platform, enterprise security teams are able to manage multiple security controls and compliance audits smoothly.
Take the team at Speedoc:
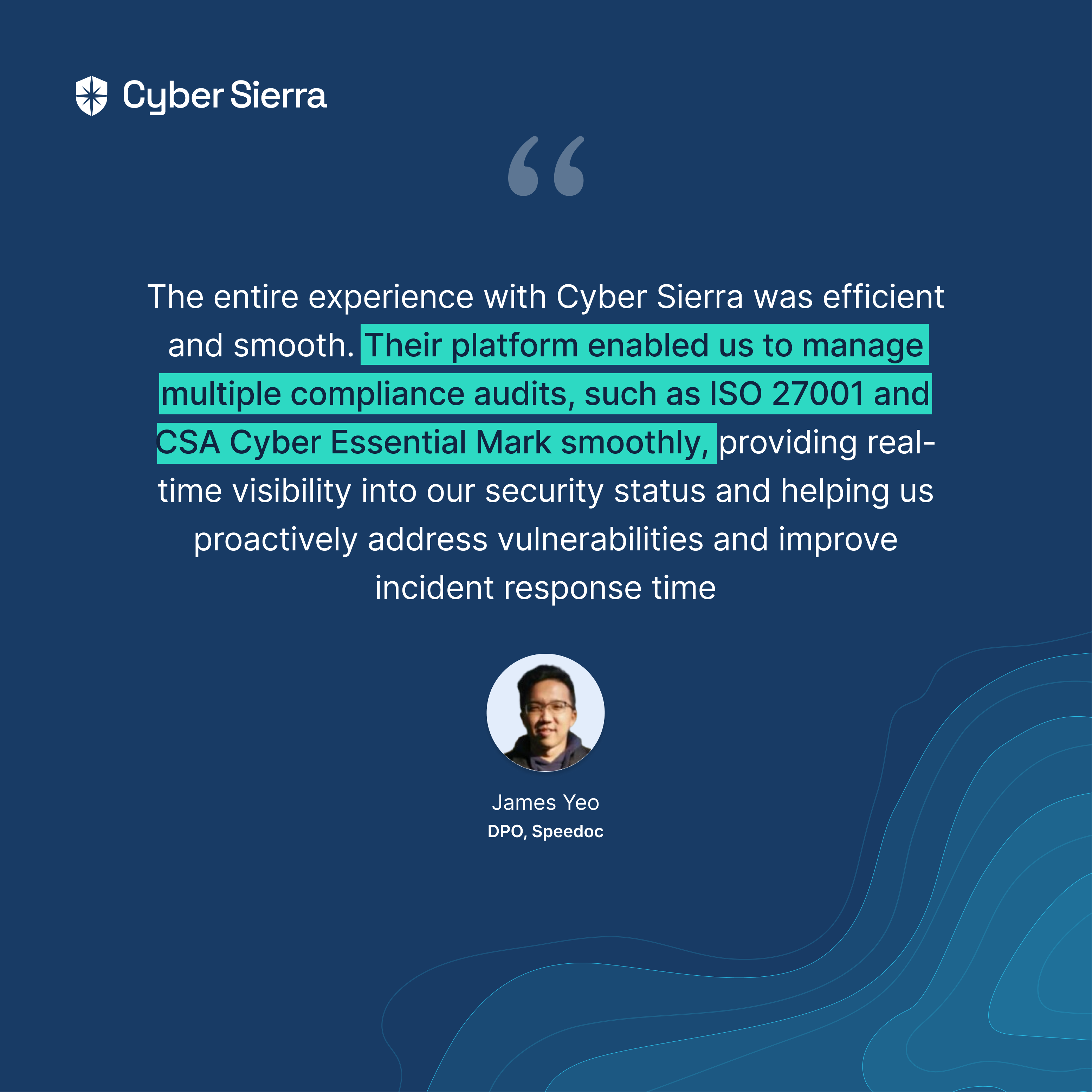
Read the example (and use case) of Speedoc here.
2. Cyber Threats’ Remediation
Cyber threats could be external, from hackers looking for misconfiguration to exploit in your IT systems. It could also be internal, from your employees leaving vulnerabilities through which cyber thieves can exploit and steal critical data.
As a result, there’s a need to have a comprehensive overview of your IT, network, and cloud assets. Specifically, you want to continuously find and fix misconfigurations or user behaviors that could lead to data breaches. Doing both simultaneously is how your security team can better secure company and users’ information. This is another example (and critical use case) of a cybersecurity CCM platform.
Speedoc leans on Cyber Sierra for this, too:
3. Vendor Risk Management
Vendors will go the extra mile, checking off all security requirements to win a company’s business. But don’t trust them to consistently secure company data once they become part of your company’s 3rd party ecosystem.
This makes ongoing vendor assessments a vital example (and use case) of cybersecurity continuous control monitoring. Using a CCM platform with vendor risk management capabilities, enterprises monitor vendors’ security posture in real-time.
Consider this global bank using Cyber Sierra:
More on this example (and use case) here.
Automating Cybersecurity Continuous Monitoring Activities In One Platform
Done separately, each example of using cybersecurity continuous control monitoring comes with loads of activities. But with an interoperable cybersecurity CCM platform, activities related to monitoring of controls can be automated from one place. This saves your security team more time to focus on more strategic endeavors of securing the company.
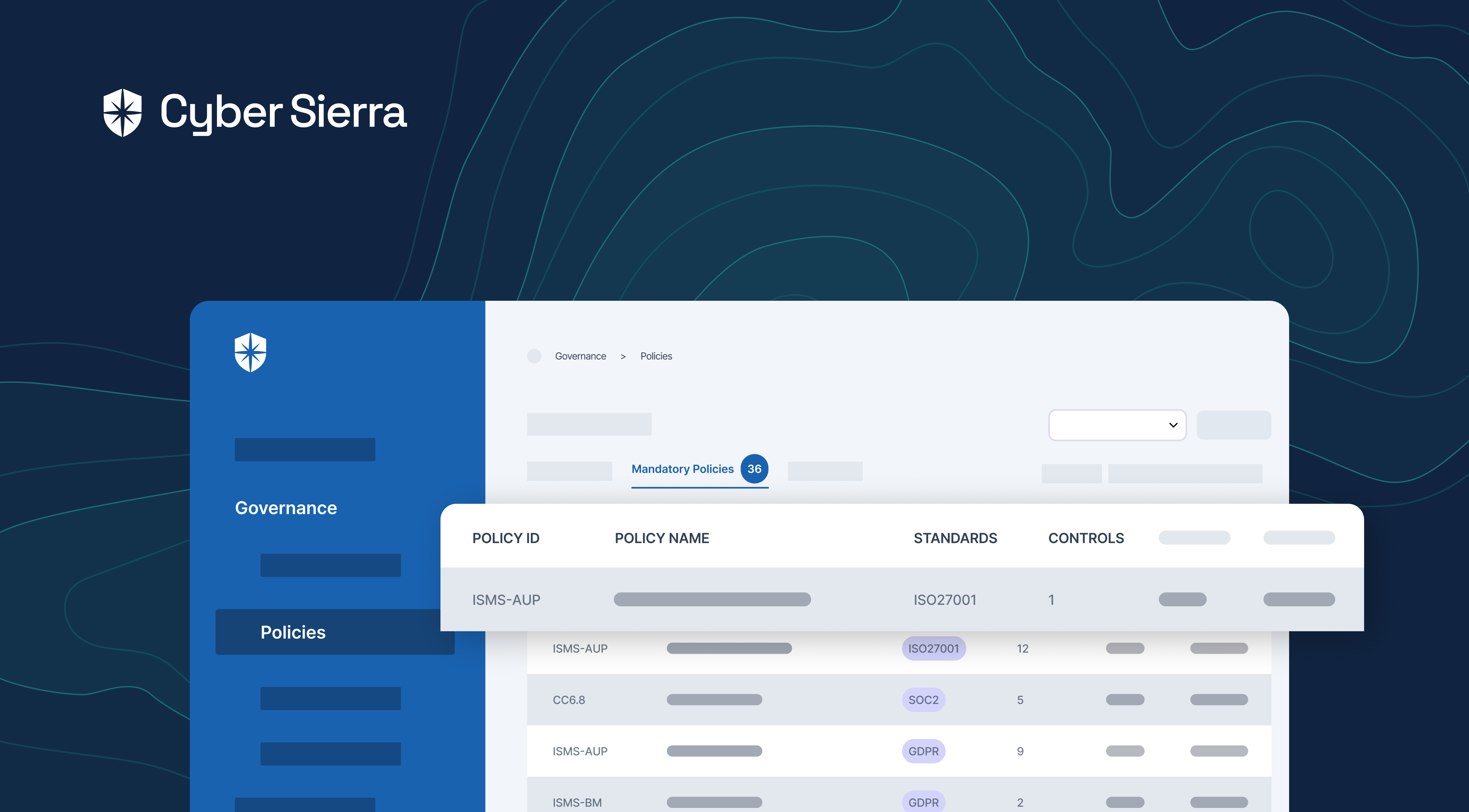
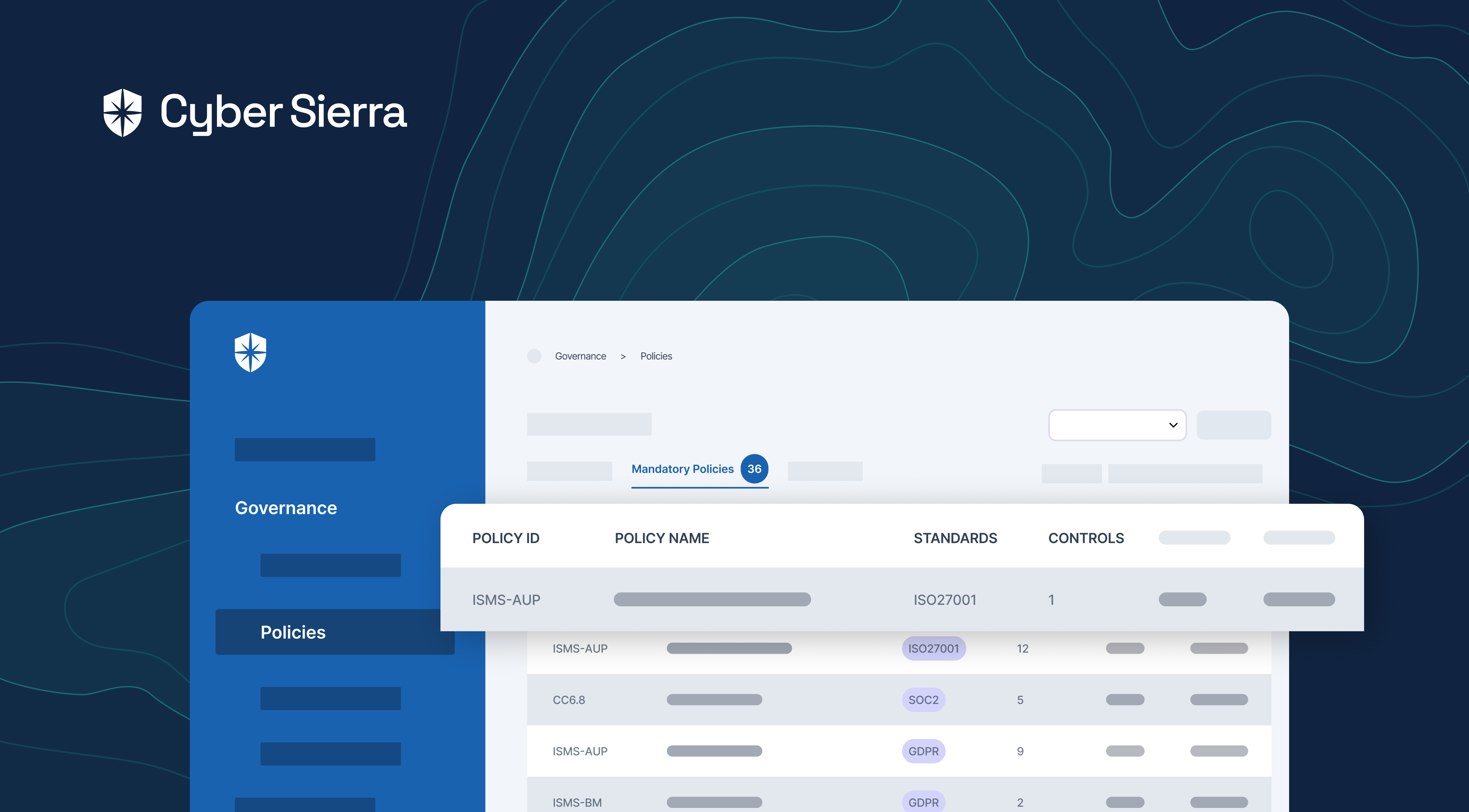
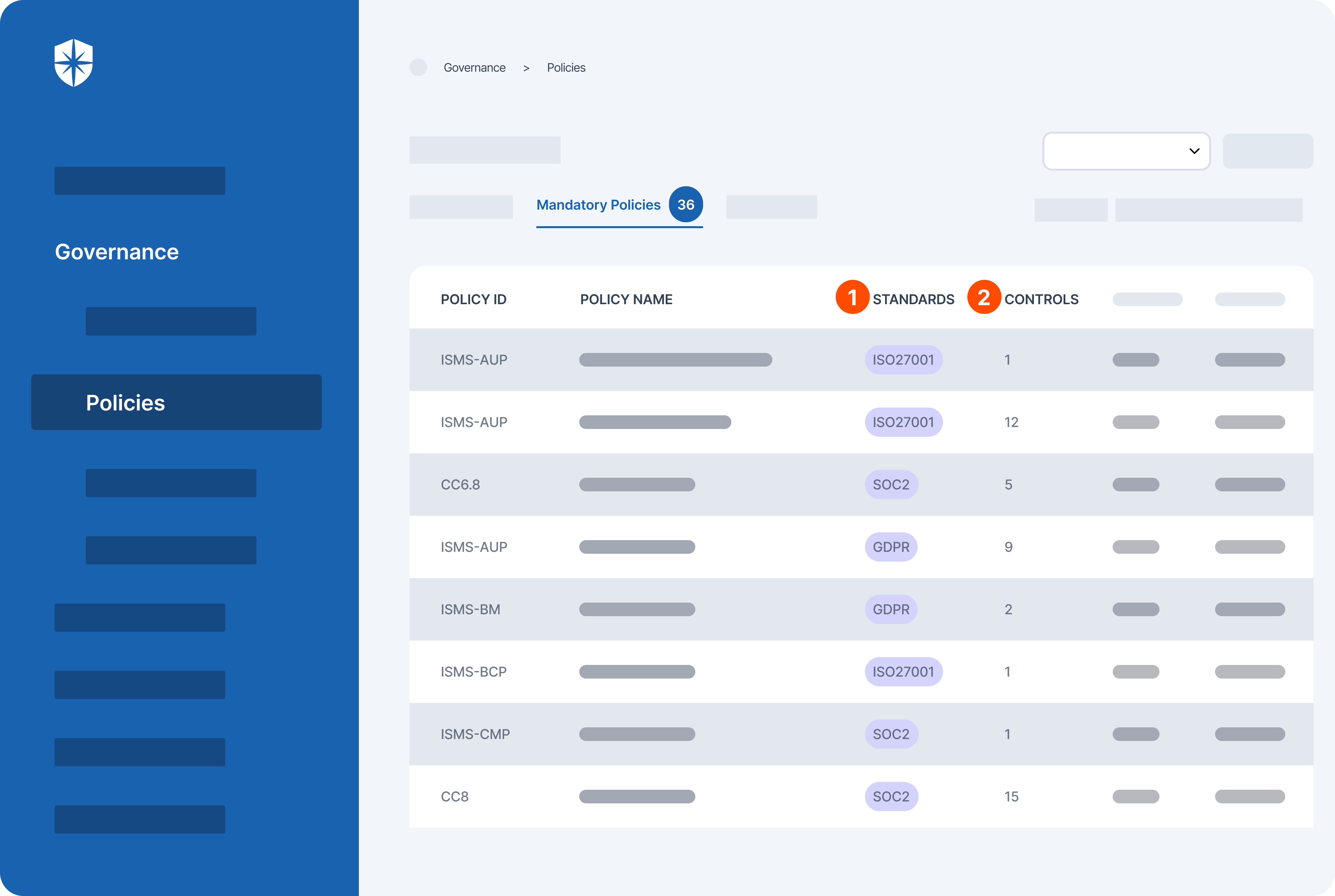
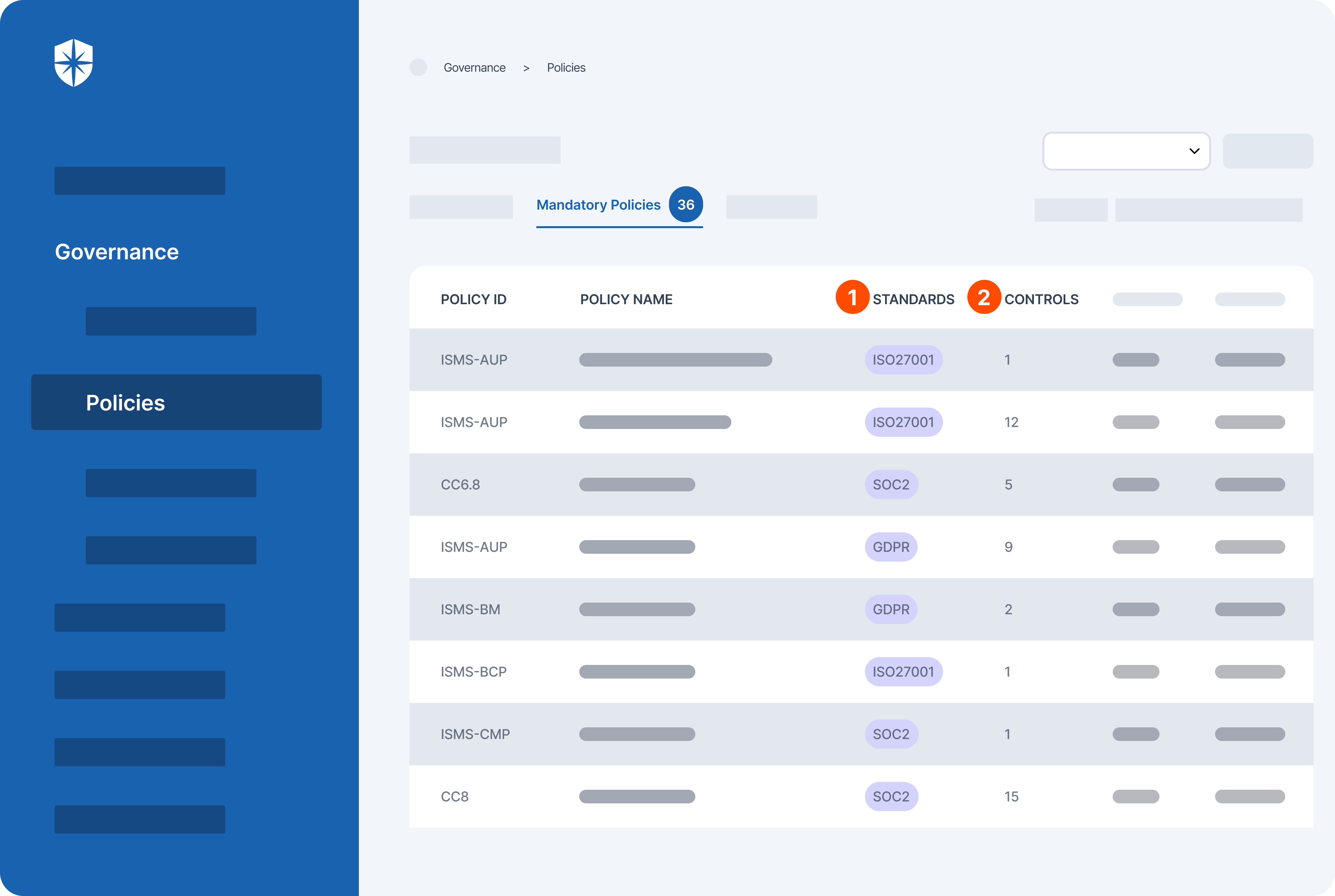
Say you wanted to instill automation in your enterprise compliance management and continuously monitor controls. With Cyber Sierra, you get access to all the popular compliance programs, along with each one’s mandatory policies (1) and security controls (2):
It doesn’t end there.
Our platform even automates the process of continuously monitoring security controls of all implemented compliance programs. This enables your compliance team to get notified whenever there are control breaks.
Here’s a peek:
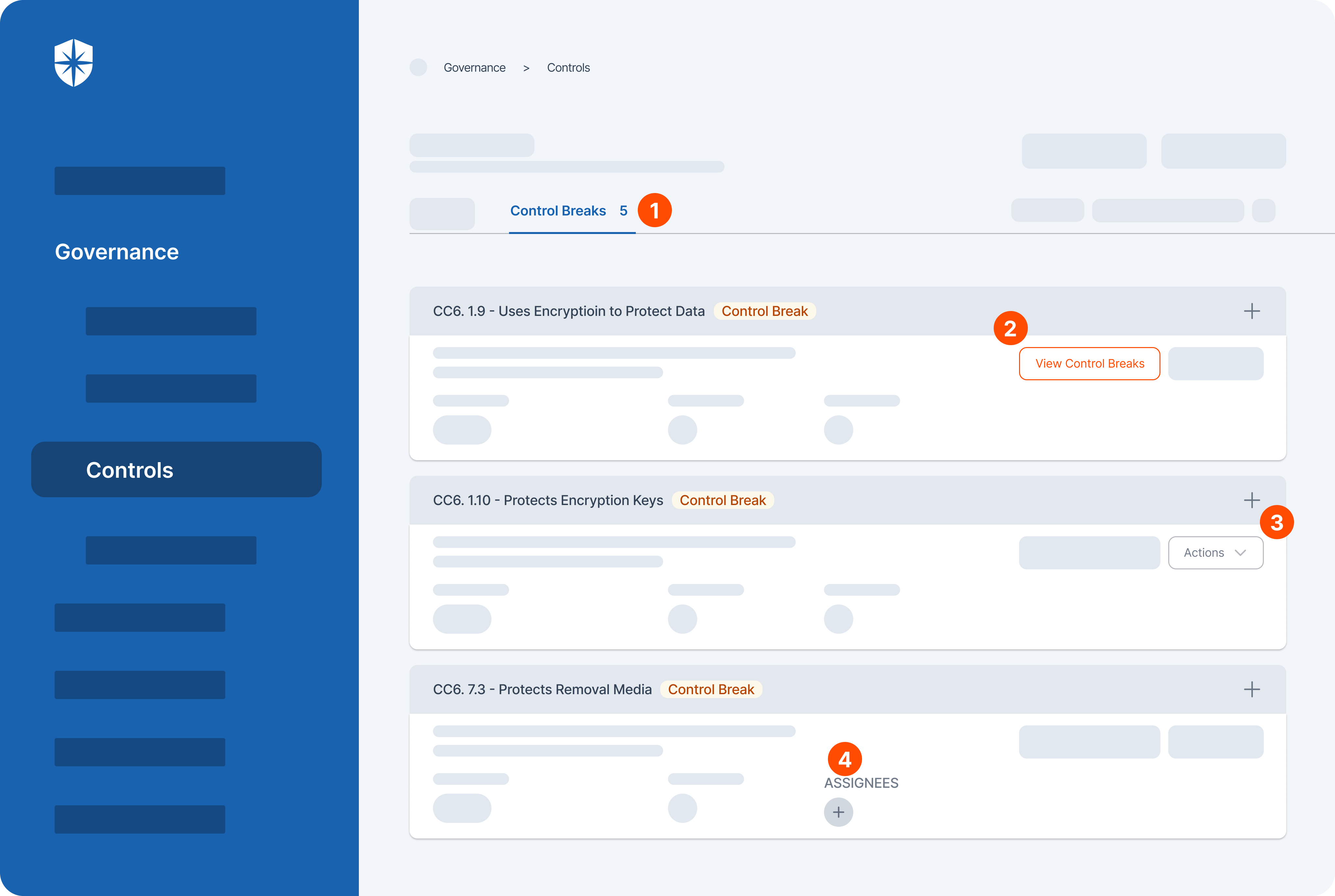
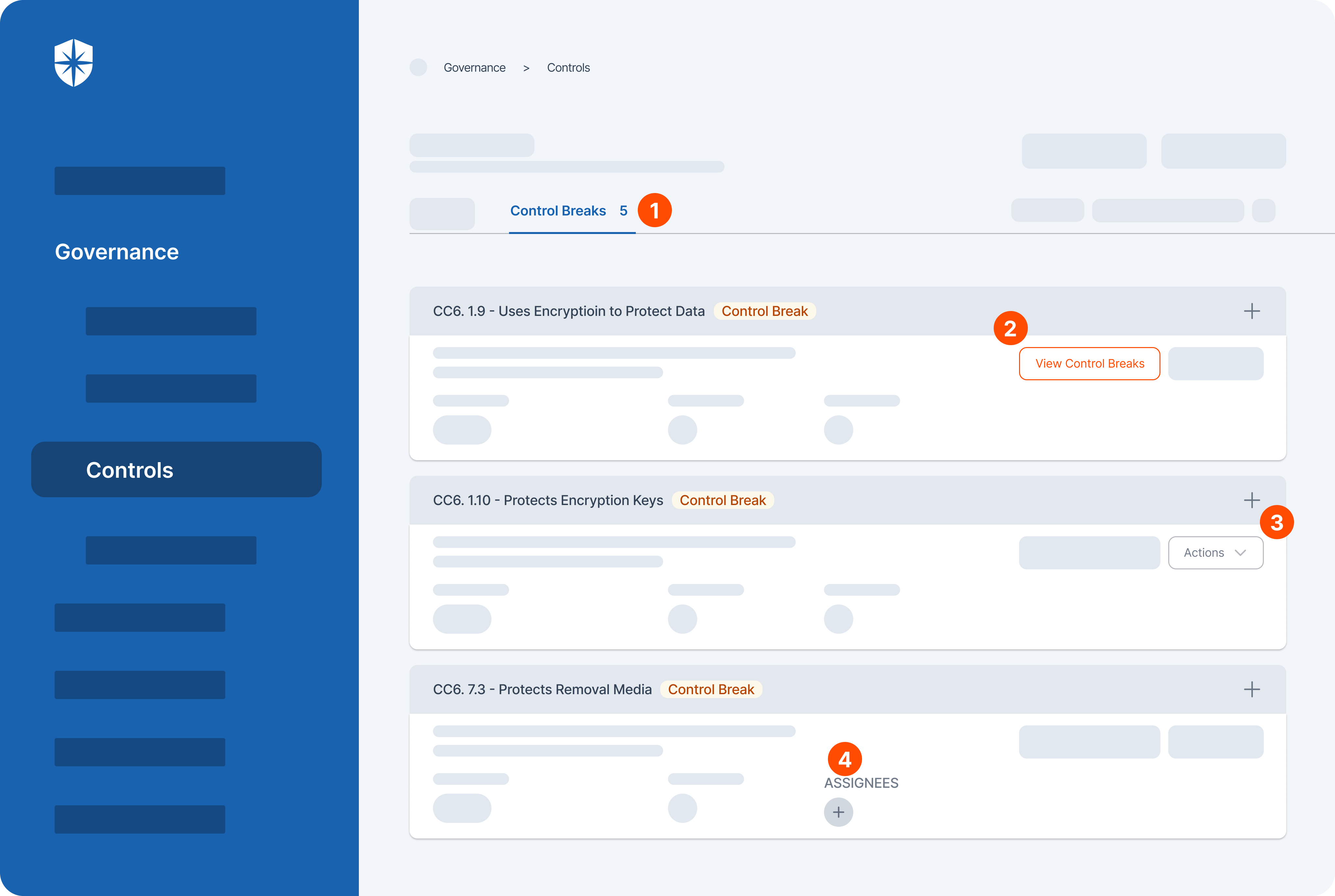
As shown, activities this streamlines in one view include:
- Monitoring control breaks of all compliance programs
- Viewing details of each control break
- Getting tips for remediating each control break, or
- Assigning remediation members of your security team.
CCM activities related to cyber threats’ remediation and vendor risk management also need to be automated. And with Cyber Sierra, your security team can monitor a range of controls from the same place.
Take cyber threats’ remediation.
Our platform lets you integrate and connect all IT, network, and cloud assets used across your organization. Once integrated, it continuously monitor and pulls data into a Risk Register, where misconfigurations and user behaviors that could cause breaches are flagged in real-time:
Our platform lets you integrate and connect all IT, network, and cloud assets used across your organization. Once integrated, it continuously monitor and pulls data into a Risk Register, where misconfigurations and user behaviors that could cause breaches are flagged in real-time:
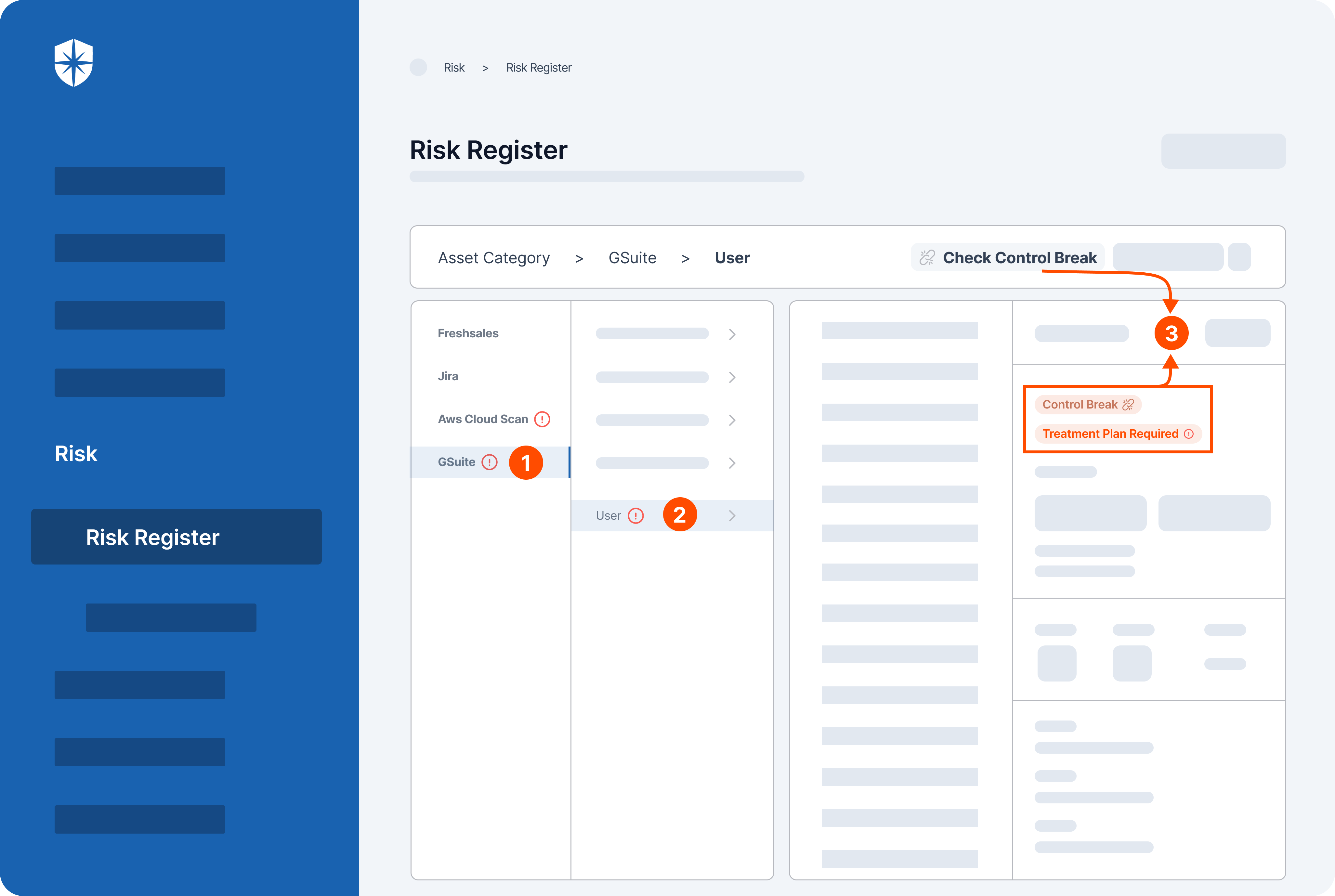
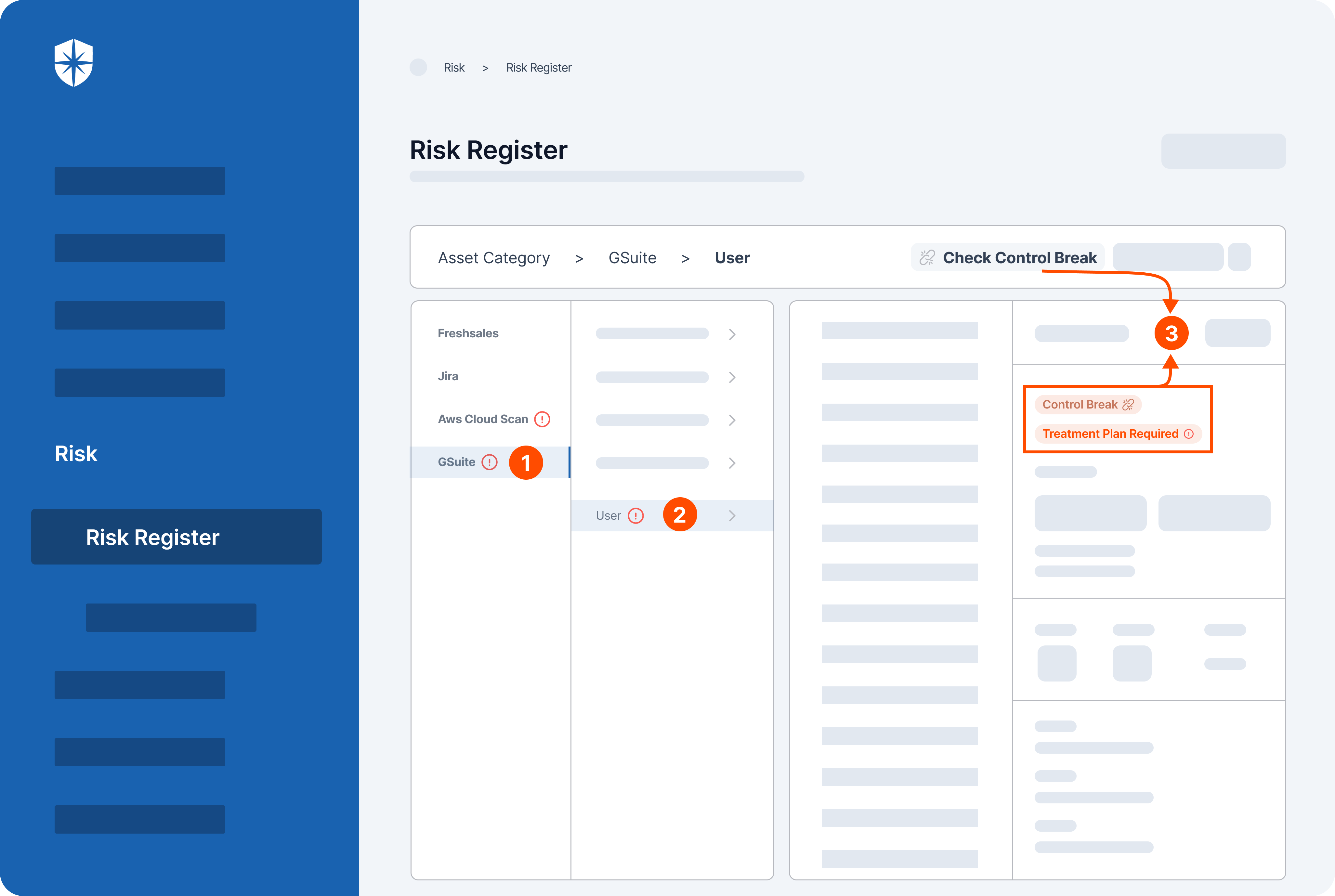
In this view, our Risk Register detected a vulnerable control break (3) by a user (2) of the GSuite cloud asset (1) automatically.
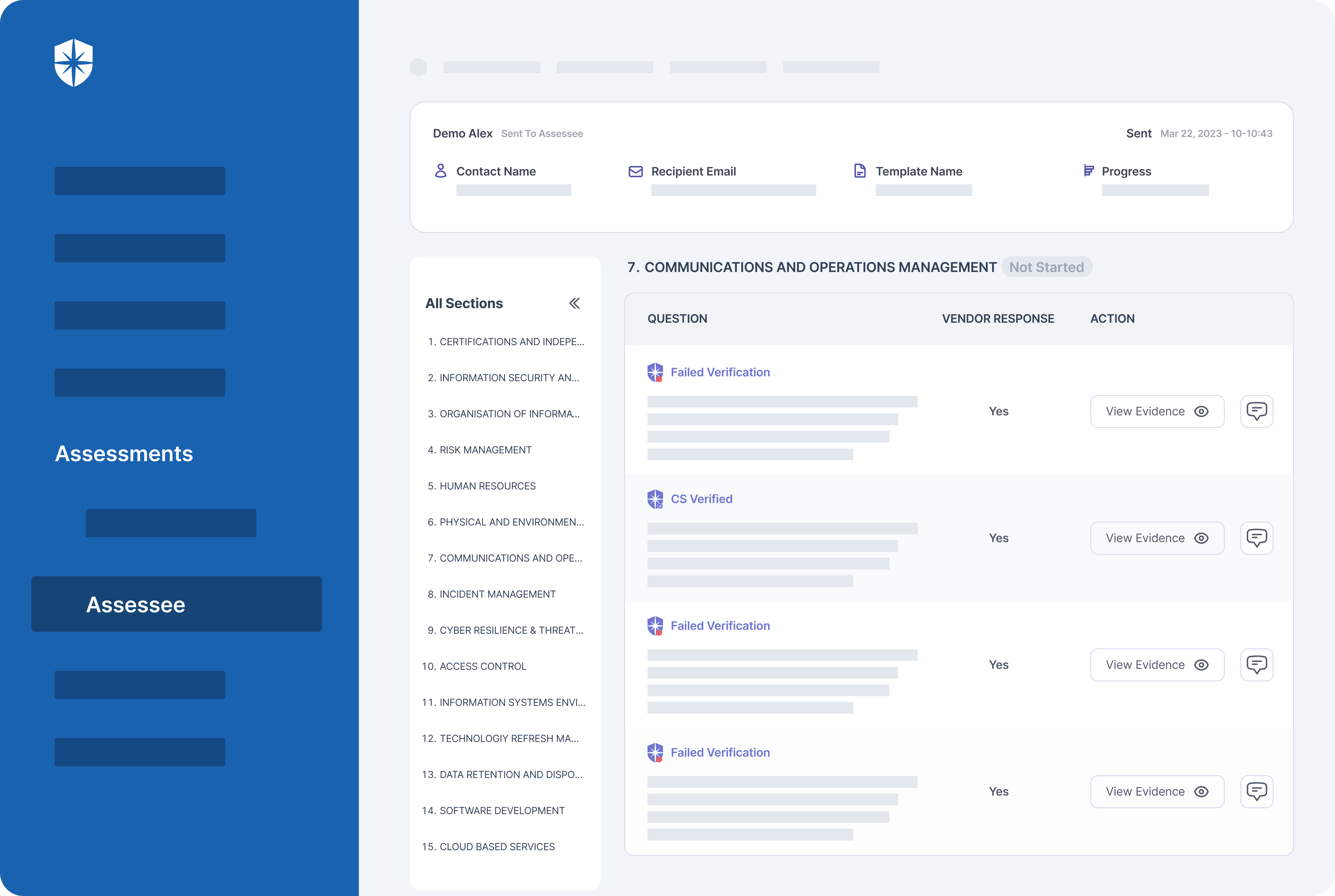
Last but not least are continuous control monitoring activities for third-party risk management. Identifying and mitigating vendor risks can be a handful, as your team must analyze, assess, and monitor 3rd parties’ security postures in real-time. This is why we built Cyber Sierra to enable enterprise security teams to do it all in one place.
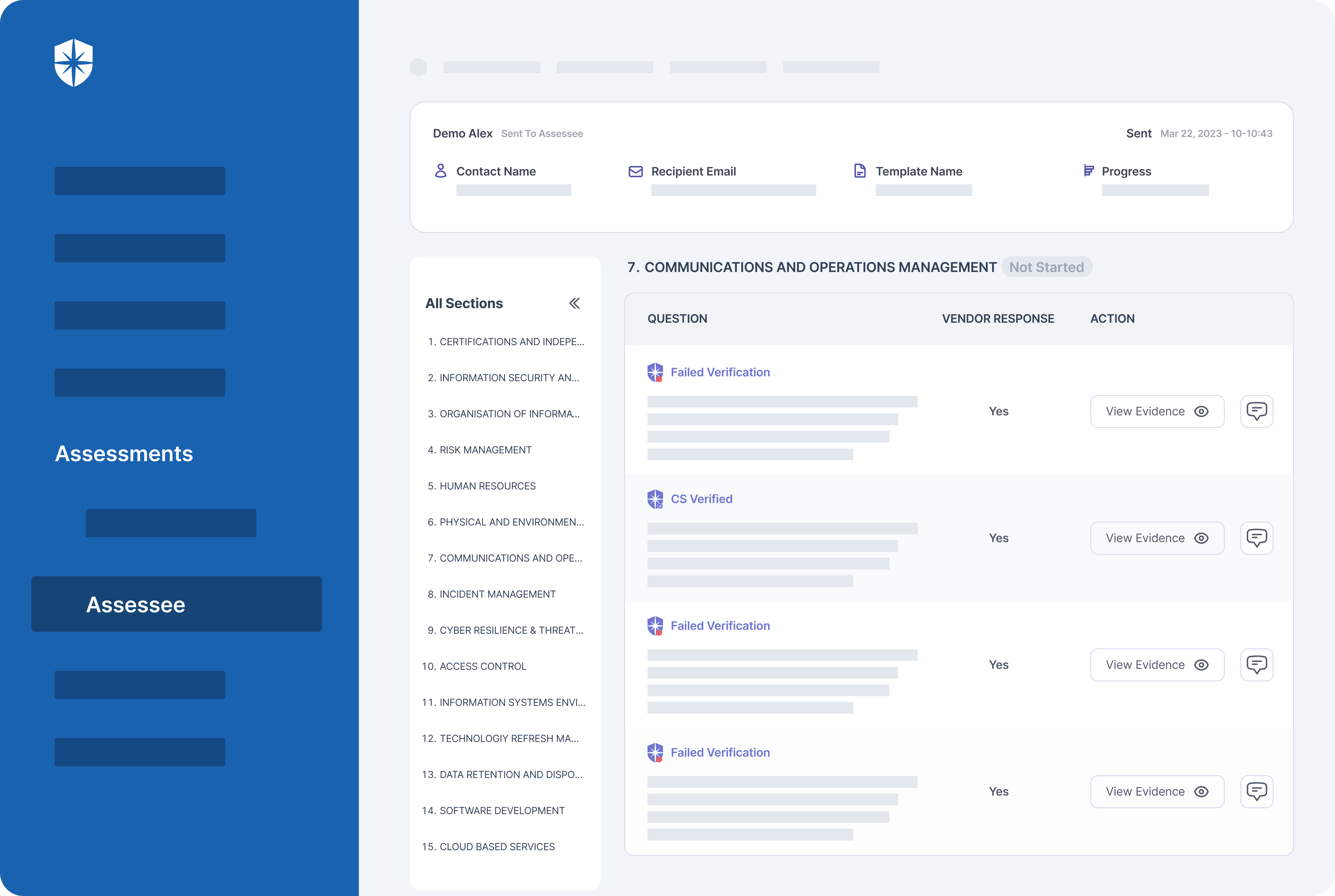
Our platform’s TPRM capability automatically and continuously assesses evidence of security controls uploaded by vendors. It is also intelligent enough to flag vendors whose evidence fail verification:
Automate Continuous Monitoring Activities
The activities involved in cybersecurity continuous control monitoring can be daunting, especially if tackled manually or from different tools. But by automating them from a single platform, enterprises can constantly monitor and get full visibility needed for the proper implementation of security controls.
That’s a reason executives at enterprise tech companies rely on a pure-play cybersecurity CCM platform like Cyber Sierra. One example is Aditya Anand, the CTO of Hybr1d. Their security team monitors and gets full visibility of security controls with our platform.
In Anand’s own words:
Hybr1d demonstrates that the many activities of cybersecurity CCM can be automated with an interoperable platform like Cyber Sierra.
Your team can achieve the same:



A weekly newsletter sharing actionable tips for CTOs & CISOs to secure their software.
Thank you for subscribing!
Please check your email to confirm your email address.
Find out how we can assist you in
completing your compliance journey.